
Hey 👋, Cyber Friends!
welcome to Cybersecurity Newsletter of the Weekaims to inform and empower in the ever-changing world of cyber threats.
In today’s issue, we cover some interesting developments in the cybersecurity landscape, each sharing insightful analysis that can help you protect yourself from potential attacks.
1. Apple 📱 devices hacked with new zero-day bug – update ASAP!
Did you recently update your Apple device? If not, the tech giant just released security updates for iOS, iPadOS, macOS, and Safari, so it’s time to do so. This update is intended to fix a zero-day vulnerability that hackers have been exploiting.
This vulnerability is tracked as CVE-2023-23529 and is related to the type confusion bug in the WebKit browser engine. What does this mean? This means that visiting a website that contains malicious code could activate the bug and result in arbitrary code execution. This means hackers can hijack your device and access all your data.
It’s scary to think that just visiting a website can lead to a security breach. This is why keeping your device up to date with the latest security patches is essential.
2. Don’t be the next victim: ESXiArgs Ransomware 💥 Hits 500+ New European Targets
Another well crafted comprehensive coverage by Ravie Lakshmanan.
A recent discovery by cybersecurity firm Censys has over 500 hosts fallen victim to the ESXiArgs ransomware strain. Most of these compromised hosts are located in France, Germany, Holland, UK, and Ukraine. Of particular concern, Censys discovered two of his hosts with ransom notes dating back to mid-October 2022, shortly after ESXi versions 6.5 and 6.7 reached the end of their life.
This means that the attackers behind ESXiArgs have been active for months and were able to gain a foothold while these hosts were not receiving security updates or patches. It also shows that ransomware attacks can take time to gain momentum, often going undetected for months before being discovered.
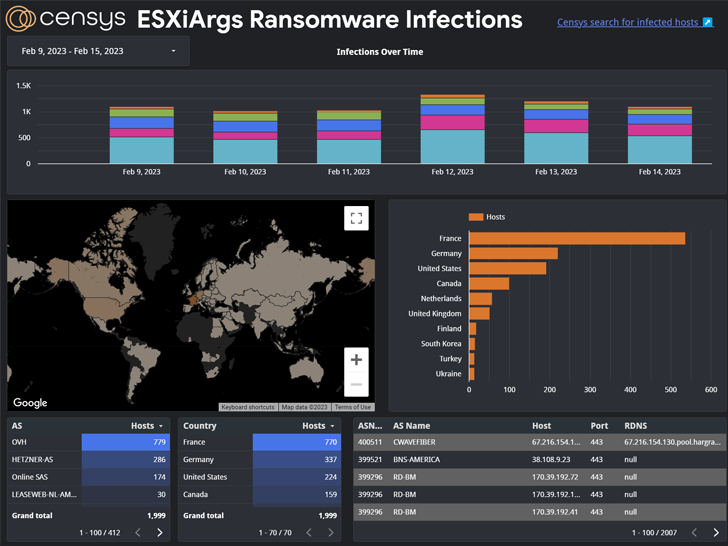
Even more alarming, the two hosts’ ransom notes were updated on January 31, 2023 to produce revisions that match those used in the current wave of attacks. This suggests that attackers are refining their tactics and making their ransomware strains better and more effective.
Ransomware attacks like ESXiArgs can wreak havoc on an organization, causing data loss, financial loss, and reputational damage. It’s important for organizations to stay vigilant and ensure that their systems are always up to date with the latest security patches and updates.
Additionally, a solid backup and disaster recovery plan can help your organization recover from attacks quickly and minimize their impact.
3. DDoS attack breaks record – 71 million 😮 requests per second!
Web infrastructure company Cloudflare reports success in thwarting a large-scale distributed denial of service (DDoS) attack. Peaking at over 71 million requests per second, the attack was the largest HTTP DDoS attack ever recorded, breaking the previous record of 46 million requests per second.
This attack was so large that Cloudflare refers to it as a “very high volume” DDoS attack. The attack targeted websites protected by Cloudflare’s platform, and the attack is believed to have originated from a botnet made up of his over 30,000 IP addresses from various cloud providers.
This attack is a reminder that DDoS attacks remain a significant threat to websites and online services, and it is important for businesses to take robust security measures to protect against such attacks.
Subscribe to our daily newsletter
We hope you enjoy reading our weekly cybersecurity newsletter. But we also understand the importance of staying abreast of the latest threats and vulnerabilities that can wreak havoc on your digital life.
Therefore, we highly recommend subscribing to our daily news updates by email. Get the latest cybersecurity news, insights, resources, offers and analysis delivered straight to your inbox every day.
4. Microsoft 🖥️ Releases Emergency Patch – Update Windows ASAP!
Microsoft has been busy this week, releasing security updates that fix a whopping 75 vulnerabilities in their products. This is the many ways cybercriminals can wreak havoc on our devices and systems!
Three of the flaws have already been exploited, so it’s important that users update their software as soon as possible. A total of nine vulnerabilities are rated as critical. This means that an attacker can remotely take over your device.
But wait. 37 of the flaws are known as Remote Code Execution (RCE) vulnerabilities. These are particularly dangerous as they allow an attacker to execute code on the victim’s device without any manipulation or permission.
Therefore, if you are using any Microsoft product, we recommend that you update as soon as possible.
5. Linux 🐧 and IoT devices under attack by V3G4 Mirai botnet
A new variant of the infamous Mirai botnet has been discovered, wreaking havoc in the world of Linux and IoT devices. Dubbed his V3G4 by experts from Palo Alto Networks Unit 42, the new version leverages 13 security vulnerabilities to spread widely.
As you know, the Mirai botnet has a notorious history and has carried out some high-profile attacks in the past. This new variant only emphasizes the importance of keeping your device and system up to date with the latest security patches and countermeasures.
6. Your Favorite Apps May Carry Dangerous Viruses – 🚨 Stay Vigilant!
Cybercriminals have launched a new type of attack targeting Chinese-speaking individuals in Southeast and East Asia. They use deceptive Google Ads to trick people looking for popular applications like Google Chrome, WhatsApp, Skype, etc. into fake websites that download malware on their machines.
This attack is particularly insidious as it uses seemingly legitimate Google ads to lure victims. The downloaded malware is a remote access Trojan called FatalRAT, which gives the attacker complete control over the infected machine.
Security researchers urge people to be careful when downloading applications, especially from unfamiliar websites.
The Hacker News / Upcoming Webinars
Tired of falling victim to file-based threats and not knowing how to protect your sensitive data? Or are you struggling to keep up with the ever-evolving security challenges of your SaaS applications?

Don’t worry. We have two exciting webinars coming up soon. This webinar will help debunk some common misconceptions and tackle the biggest security challenges of 2023.
- First webinar “MythBusting Special: 9 Misconceptions About File-Based Threatshelps separate fact from fiction when it comes to file-based threats. Learn the truth about what they are, how they work, and most importantly, how to prevent them from breaking into your system.
- Also, if you’re a fan of SaaS applications but still grappling with security issues, check out our second webinar “How to Tackle the Top SaaS Security Challenges of 2023“, it’s for you! Our experts walk you through the most pressing security challenges of 2023 and offer actionable tips to help you stay ahead of your game.”
Both of these webinars are free and packed with valuable information you don’t want to miss. Sign up now to participate in informative and engaging cybersecurity discussions!
That’s it for this week’s cybersecurity newsletter.
As always, remember that cybersecurity is not a one-time event or quick fix. Every little thing, like using strong passwords, updating your software regularly, and being aware of phishing scams, can make a big difference in protecting your online security.
So keep these firewalls and keep updating them. Stay curious, vigilant, and safe in the ever-changing digital landscape.
And above all, remember that cybersecurity is a community effort. We look forward to hearing from our readers. We are always ready to answer your questions and address your concerns. If you have any suggestions for topics you would like us to cover in future newsletters, please let us know.
Thank you for joining us on this cybersecurity journey. We look forward to sharing more insights and updates in the coming weeks. Until next time, keep up the cybersecurity!











