Cybersecurity researchers have discovered a PlugX sample that fraudulently infects attached removable USB media devices and spreads malware to additional systems.
Palo Alto Networks Unit 42 researchers Mike Harbison and Jen Miller-Osborn said: “Users don’t know that their USB devices may be infected or used to exfiltrate data from the network.”
A cybersecurity firm said it discovered the artifact during incident response efforts following the Black Basta ransomware attack against an unnamed victim. Other tools found in compromised environments include the Gootkit malware loader and the Brute Ratel C4 red team framework.
The Black Basta group’s use of Brute Ratel was previously noted by Trend Micro in October 2022, with the software delivered as a second stage payload by a Qakbot phishing campaign. This attack chain has since been used against a large regional energy organization based in the southeastern United States, according to Quadrant Security.
However, there is no evidence linking PlugX, a backdoor widely shared by several national groups in China, or Gootkit to the Black Basta ransomware gang, suggesting that it may have been deployed by other actors. increase.
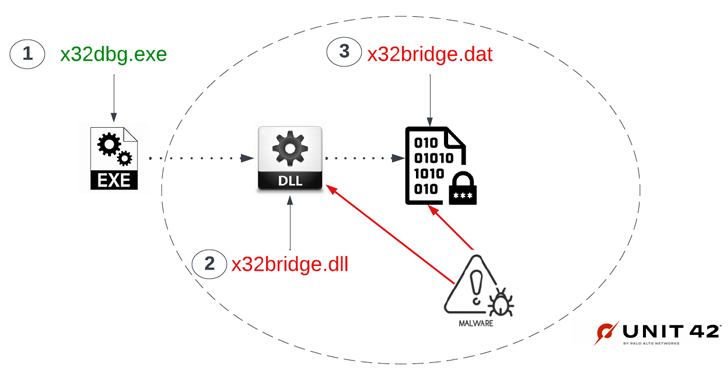
The USB variant of PlugX is notable for the fact that it uses a specific Unicode character called a non-breaking space (U+00A0) to hide files in USB devices attached to the workstation.
“Whitespace prevents the Windows operating system from rendering directory names, hiding unnamed folders rather than leaving them in Explorer,” the researchers said, explaining the new technique.
Ultimately, it uses a Windows shortcut (.LNK) file created in the root folder of the flash drive to run the malware from a hidden directory. In addition to embedding malware on the host, the PlugX sample is also tasked with copying malware to potentially attached removable devices by disguising itself within the Trash folder.
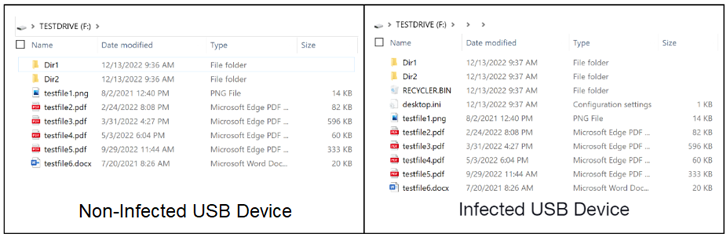
The shortcut file has the same name as the USB device and appears as a drive icon. Any existing files or directories in the root of the removable device will be moved to a hidden folder created inside the “Shortcuts” folder. .
“Every time an infected USB device shortcut file is clicked, the PlugX malware launches Windows Explorer and passes the directory path as a parameter,” said Unit 42. “Then view the files on her USB device from within a hidden directory and infect the host with her PlugX malware.”
This technique is based on the fact that Windows File Explorer (formerly Windows Explorer) does not show hidden items by default. But a neat twist here is that malicious files in the so-called Recycle Bin are not visible when the setting is enabled.
This effectively means that the malicious files can only be viewed in a Unix-like operating system like Ubuntu or by mounting the USB device in a forensic tool.
“When a USB device is discovered and infected, any new files written to the root folder of the USB device after infection are moved to a hidden folder within the USB device,” said the researchers. “Unwittingly he continues to spread the PlugX malware because Windows shortcut files are similar to USB device shortcut files and the malware displays the victim’s files.”
Unit 42 also said they found a second variant of PlugX. This variant not only infects the USB device, but also copies all Adobe PDF and Microsoft Word files from the host to another hidden folder on the USB device created by the malware.
The use of USB drives as a means of exfiltrating specific files of interest from targets indicates that some attackers are attempting to jump over air-gapped networks.
With its latest development, PlugX joins other malware families such as ANDROMEDA and Raspberry Robin that have added the ability to spread via infected USB drives.
“The discovery of these samples indicates that PlugX development is still alive and well among at least some technically adept attackers and remains an active threat,” the researchers conclude. increase.











