Cybersecurity researchers have discovered the real-world identity of the threat actor behind it golden chicken Malware-as-a-service using the online persona “badbullzvenom”.
eSentire’s Threat Response Unit (TRU) “found multiple mentions of the badbullzvenom account being shared between two people,” in an exhaustive report released after a 16-month investigation. says.
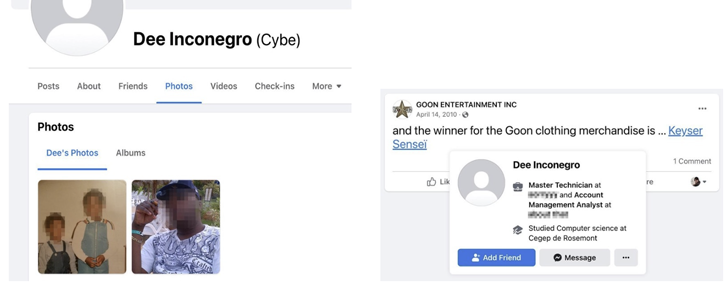
A second threat actor, known as Frapstar, is said to call itself “Chuck of Montreal” to help cybersecurity firms piece together the digital footprints of criminals.
This includes his real name, photo, home address, names of his parents, siblings, friends, social media accounts and interests. He is also said to be a sole proprietor of a small business he runs from his home.
Golden Chickens, also known as Venom Spider, is a Malware as a Service (MaaS) provider and has been linked to various tools such as Taurus Builder, a software that creates malicious documents. More_eggs is a JavaScript downloader used to deliver additional payloads.
The threat actor’s cyberweapon has been used by other prominent cybercriminal groups such as the Cobalt Group (aka Cobalt Gang), Evilnum, and FIN6, all of which are estimated to have caused $1.5 billion in combined losses. .
Previous More_eggs campaigns (partially dating back to 2017) involved spear-phishing business professionals on LinkedIn who offered fake job offers that allowed threat actors to remotely control a victim’s machine, which they It was used to gather information and even deploy malware.
Last year, in a reversal of sorts, the same tactic was employed, where a corporate hiring manager was attacked with a résumé that contained malware as an infection vector.
The earliest record of Frapster’s activity dates back to May 2015, when Trend Micro described him as a “lone criminal” and luxury car enthusiast.
“Using multiple aliases for underground forums, social media, and Jabber accounts, ‘Chuck’ and threat actors claiming to be from Moldova have gone to great lengths to disguise themselves,” it said. said eSentire researchers Joe Stewart and Keegan Kaeplinger.
“They also went to great lengths to obfuscate the Golden Chickens malware, making it undetectable by most AV companies and restricting customers to using Golden Chickens for targeted attacks only.”
Chuck is suspected to be one of two threat actors operating the badbullzvenom account on the Exploit.in underground forum, possibly in Moldova or Romania, eSentire points out .
A Canadian cybersecurity firm has uncovered yet another new attack campaign targeting e-commerce companies, saying it tricked recruiters into downloading malicious Windows shortcut files from websites masquerading as resumes.
Shortcut, a malware called VenomLNK, acts as an initial access vector to drop More_eggs or TerraLoader, which is then followed by TerraRecon (for victim profiling), TerraStealer (for information stealing) and TerraCrypt (for victim profiling). It acts as a conduit for deploying various modules. ransomware extortion).
“This malware suite is still in active development and is being sold to other threat actors,” the researchers concluded, urging organizations to be on the lookout for potential phishing attacks.











