Challenges of enforcement-based approaches
An enforcement-based approach to security begins with a security policy backed by security controls. Security controls are often designed to prevent employees from engaging in risky behavior and inadvertently increasing an organization’s potential attack surface.
Most organizations use only enforcement-based security controls, typically performed at the network level using a Cloud Access Security Broker (CASB) or Security Services Edge (SSE). A CASB protects data between on-premises and cloud architectures, validates authorization rules, and enforces access control against company security policies. Some organizations use CASBs to block SaaS applications, but like SSEs, CASBs only provide support. Several application.
Application These tools please do not Support is often the most risky because it doesn’t meet common industry and security standards like SAML for authentication and SCIM for user management. At Cerby, we call these “unmanageable applications” and according to their research: 61% of SaaS applications are unmanageableHard-to-manage applications are popular, and in the post-COVID world, the speed at which employees purchase and deploy applications is reaching new heights.
Prior to COVID, IT departments were primarily responsible for purchasing and deploying applications across the organization. The shift to remote work has allowed employees to choose their own tools across the organization. At the same time, rapid digitization has created an ever-growing array of tools to choose from and a proliferation of unmanageable applications.
The average user usually doesn’t think security first. Most people tend to think their applications are secure, and some people don’t care about security at all. Most users care about easy-to-use features, aesthetics of design, and convenience. To meet these changing requirements, application vendors have changed their product roadmaps. Security was no longer a top priority for many of them.
Whether employees know it or not, unmanageable applications can negatively impact an organization’s security and often create more work for technology teams. who Unmanageable applications must be monitored, features such as two-factor authentication (2FA) manually enabled, and strong passwords enforced.
To ease this burden, many organizations block or ban applications they cannot manage.
I completely understand why organizations take this approach. It’s a quick and consistent way to address pressing concerns. However, as a long-term comprehensive solution, a purely coercion-based system is neither sustainable nor practical.
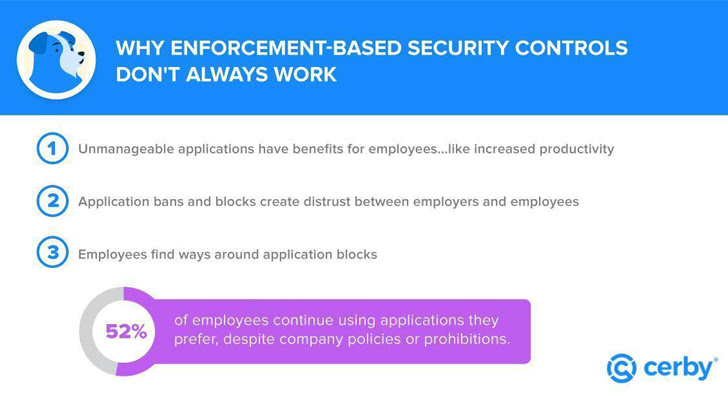
Employees like to select work applications and 92% of employees and managers want full control over application selectionThis change in behavior poses unexpected challenges for organizations adopting an enforcement-based approach.
For example, many employees using banned or blocked applications try to manage access manually, even if they are not equipped to do so. Our research shows that employees and managers have access controls that introduce risk and exposure to organizations at every point of interaction.
So what is the solution? A more pragmatic, forward-looking attitude that balances employee application choices with employer priorities such as security and compliance.
Advantages of a registration-based approach
A registration-based cybersecurity approach empowers employees with greater freedom and personal autonomy and choice, enabling them to actively participate in enterprise-wide security and compliance efforts. Unlike mandatory-based systems, a registration-based approach allows employees to choose which applications they use for work.
Cerby was born in response to an unmet need for a solution that balances enforcement and registration, allowing security and autonomy to coexist peacefully. Striking this balance is the best answer for both your organization and your employees.employees should be able Choose Employers don’t have to worry about security.
Security becomes everyone’s concern when employees understand that choosing an application is a responsibility, and when the right tools are readily available to make this happen. The same employees who are frustrated by policies regarding application choice will gladly accept easier and enhanced security, along with the benefits of compliance, if they have access to self-enrollment and enrollment applications.
Check out this report to learn more about how you can give your employees the freedom to use their favorite apps and how Cerby makes it easy to keep them safe.











