A North Korean threat actor known as the Lazarus Group has been observed shifting its focus and rapidly evolving its tools and tactics as part of a long-running operation dubbed “Lazarus Group.” death note.
The nation-state adversary is known for its ongoing attacks on the cryptocurrency sector, but has also targeted the automotive, academic and defense sectors in Eastern Europe and other parts of the world, viewed as a “key” pivot. It is done.
“At this point, the attackers switched all decoy documents to job descriptions related to defense contractors and diplomatic services,” said Kaspersky researcher Seongsu Park in an analysis released Wednesday.
Target deviation is said to have occurred in April 2020, along with the use of an updated infection vector. Note that the DeathNote cluster is also tracked under the name Operation Dream Job or NukeSped. The Google-owned Mandiant also associated a subset of the activity with his group called UNC2970.
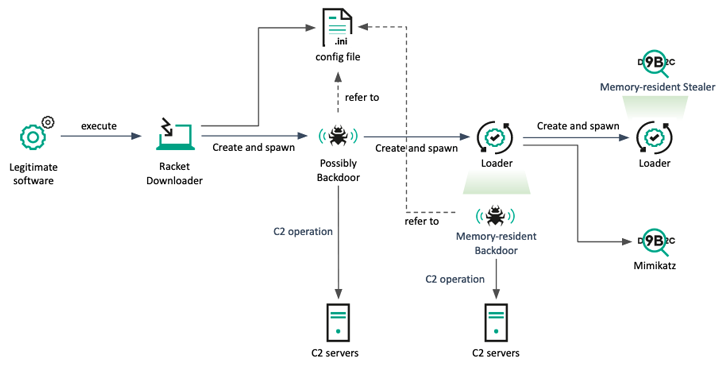
Phishing attacks against crypto businesses typically use bitcoin mining-themed lures in email messages to lure potential targets into dropping a Manuscrypt (aka NukeSped) backdoor on the compromised machine. to open a document containing macros.
As Russian cybersecurity firm documented in October 2021, targeting the automotive and academic sectors has been linked to Lazarus Group’s broader attacks on the defense industry, including BLINDINGCAN (aka AIRDRY or ZetaNile). and the deployment of COPPERHEDGE implants.
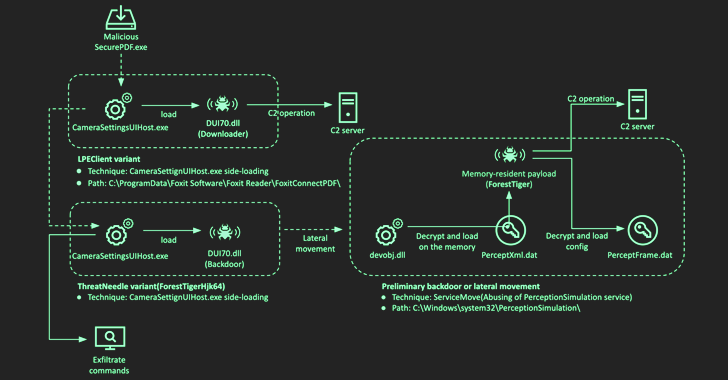
In another attack chain, threat actors used a Trojan horse version of a legitimate PDF reader application called SumatraPDF Reader to launch malicious routines. The use of rogue PDF reader apps by Lazarus Group was previously disclosed by Microsoft.
Targets of these attacks include a Latvian-based IT asset monitoring solution vendor and a South Korean-based think tank, the latter of which uses legitimate security techniques widely used in the country to execute payloads. It required software exploits.
Learn How to Secure Your Identity Perimeter – A Proven Strategy
Improve your business security in our upcoming expert-led cybersecurity webinar: Exploring Identity Perimeter Strategies!
Don’t miss it – secure your seat!
These two attacks “demonstrate that Lazarus is building supply chain attack capabilities,” Kaspersky said at the time. A hostile crew is responsible for the supply chain attack aimed at enterprise VoIP service provider 3CX that was revealed last month.
Kaspersky targeted multiple victims in South Korea in March 2022 by delivering a downloader malware that could exploit the same security software to provide a backdoor and an information stealer program to collect keystrokes and clipboard data. said it discovered another attack targeting
“The newly embedded backdoor is able to execute payloads obtained via named pipe communication,” Park said, adding, “It is also responsible for collecting and reporting victim information.” Added.
Around the same time, the same backdoor allegedly infiltrated a Latin American defense contractor using a DLL sideloading technique when opening a specially crafted PDF file using a Trojanized PDF reader. It is said
The Lazarus Group is also linked to another defense contractor breach in Africa last July. In this breach, a “suspicious PDF application” was sent over his Skype and eventually dropped a backdoor variant called ThreatNeedle and another implant known as ForestTiger to exfiltrate data. .
“The Lazarus group is notorious and highly skilled attackers,” said Park. “As Lazarus Group continues to refine its approach, it is important that organizations remain vigilant and take proactive measures to defend against malicious activity.”









