
Recent data breaches spanning CircleCI, LastPass, and Okta highlight common themes. Enterprise SaaS stacks connected to these industry-leading apps can be at serious risk of compromise.
CircleCI, for example, plays an integral SaaS-to-SaaS role in SaaS app development. Similarly, tens of thousands of organizations rely on Okta and LastPass security roles for SaaS identity and access management. Enterprise and niche SaaS apps are effectively introducing large numbers of unmonitored endpoints to organizations of all sizes.
Spending on SaaS security is on the rise, but lags behind categories such as cloud infrastructure protection and network security. According to Statista, the average organization uses over 100 of his SaaS apps, many of which are not sanctioned by IT, creating obvious gaps in SaaS security.
Why users flock to SaaS apps — and why they often bypass IT in the process
End-user behavior has changed as productivity tools for tasks such as marketing automation, document signing, and sales forecasting have moved from installed software to SaaS. The employee finds his SaaS solution to help him get more done in less time, especially as his IT function becomes more decentralized.
Employees are always looking for ways to be more productive with their tools of choice. This behavior is neither new nor malicious per se, but it poses a serious security risk. In the era of installed software, organizations add endpoint her security to work machines and devices to prevent employees from downloading harmful software or falling victim to malware-based attacks. bottom. While this approach remains an important aspect of endpoint security overall, it does not reflect the evolution of how people currently work outside the confines of corporate networks, often on personal devices.
Instead of approaching security and IT to figure out policies for onboarding new SaaS solutions, instead of facing the possibility of red tape, delays, or denied requests, break credit cards. , choose a 30-day free trial of the SaaS app. When approving new apps to connect to enterprise SaaS systems such as Microsoft 365, Salesforce, Workday, and ServiceNow, employees rarely consider the security implications of the shadow IT they’ve introduced into their ecosystem.
These connections, coupled with users’ inherited permission settings, can expose your organization’s most sensitive data, and you cannot monitor or control the risk of this attack surface. increase.
AppOmni: SaaS Security and SSPM Platform
Protect your business’ valuable data across multiple applications Powerful SaaS security management software from AppOmniGain insight and visibility to protect against potential security threats. Our state-of-the-art technology ensures protection against public exposure of his SaaS data, over-privileged external users, third-party applications, and more. Rest easy knowing your company data is in control with AppOmni. Try it today.
How SaaS apps inherit permissions via OAuth tokens
In many organizations, SaaS apps (and SaaS-to-SaaS connections) leverage OAuth access tokens both at initial connection and throughout their lifecycle. This process typically follows these steps:
- Users are authenticated to enterprise SaaS apps via simple or strong Zero Trust authentication. They are now in the SaaS cloud.
- The user wants to save time switching between project management tools and documents, spreadsheets, and email. Therefore, they are looking for ways to streamline their work. That search leads to a popular project management SaaS plugin (possibly with a free trial), and the user decides to try it.
- User initiates installation and responds to prompts granting read/write access to data and associated data within major SaaS platforms such as office productivity suites[はい]Click. There is no hierarchy of different permissions for users to choose from.
- OAuth tokens are created by the office productivity suite. This token allows project management apps and office productivity suites to maintain API-based cloud-to-cloud communication without requiring users to log in and authenticate on a regular basis.
From this point on, the project management app will be continuously connected after the initial strong authentication. CASBs and SWGs are no Discover this SaaS-to-SaaS connection.
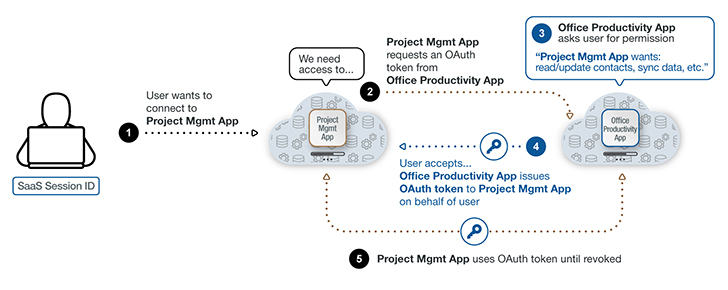 |
| Figure 1: A breakdown of how SaaS-to-SaaS connections interact with OAuth tokens. |
These application tokens are valuable because they give users easy access to the project management app. Unfortunately, they are of equal or greater value to an attacker looking for an easily exploitable entry point into her SaaS system of a company.
Reach and Risk — Existence of SaaS Apps and Inter-SaaS Connections
If an attacker successfully hijacks an OAuth token, they can compromise CRMs, code repositories, and more. A compromised he-she SaaS-to-SaaS connection could provide valid and authorized API access to many different production SaaS environments and data.
Security and IT teams are overloaded with monitoring and maintaining configuration settings and growth of enterprise SaaS platforms, let alone unapproved SaaS apps. Without a security review, SaaS-to-SaaS connections create potentially vulnerable endpoints.
The penetration of these SaaS-to-SaaS connections is substantial and often underestimated by IT organizations. According to SaaS security provider App Omni:
- The average enterprise organization has over 42 separate SaaS-to-SaaS apps connected to a live SaaS environment within the enterprise. About 50% of these apps were connected directly by end users, not by IT teams.
- About half of these 42 connected apps have not been used in the last 6 months. Connected SaaS-to-SaaS apps retain data access whether active or dormant.
- Many of these organizations have totaled about 900 user-to-application connections.
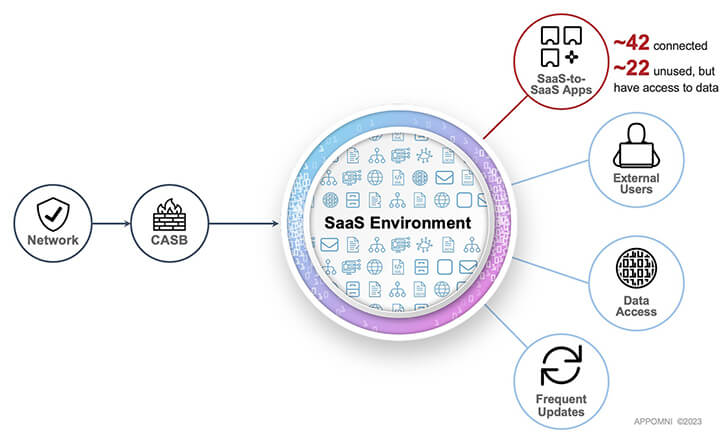 |
| Figure 2: SaaS environments include many entry points outside traditional networks and CASB protections. |
As this research shows, the number of “approved” apps that come into contact with potentially sensitive data cannot be assessed and monitored without proper SaaS security tools.
Practical steps to monitor and secure SaaS connections
Most security teams lack the right tools for visibility into SaaS connections and related user activity. SaaS Security Posture Management (SSPM) solutions address these issues by giving you visibility and control over your SaaS assets.
For example, security or IT professionals can leverage SSPM to discover everything running in Salesforce and the SaaS apps connected to it. The same is true for many of her other SaaS applications used by the organization.
This additional visibility and control over continuous monitoring of SaaS apps and SaaS-to-SaaS connections reduces attack surface risk and enables proactive security controls. If vulnerabilities are discovered, the security team can take action, such as identifying unauthorized, insecure, or over-privileged SaaS apps of hers.
Thanks to the continuous monitoring capabilities of the SSPM solution, security teams can baseline SaaS activity and use it as a point-in-time frame of reference. While the possibility of SaaS-related breaches cannot be completely ruled out, the use of an SSPM can greatly reduce that risk.









