attacker behind RTM Locker has developed a ransomware strain that can target Linux machines. This marks the group’s first foray into an open source operating system.
“The locker ransomware infects Linux, NAS and ESXi hosts and appears to have been inspired by the leaked source code of the Babuk ransomware,” Uptycs said in a new report published Wednesday. “He at Curve25519 (asymmetric encryption) uses a combination of ECDH and Chacha20 (symmetric encryption) to encrypt files.”
RTM Locker was first documented by Trellix earlier this month, describing its adversary as a private Ransomware as a Service (RaaS) provider. Its roots lie in a cybercriminal group called Read The Manual (RTM) known to have been active since at least 2015.
The group is notorious for deliberately avoiding high-profile targets such as critical infrastructure, law enforcement, and hospitals to get as little attention as possible. It also uses affiliates to demand ransom from the victim as well as exfiltrate the stolen data if the victim refuses to pay.
The Linux flavor is specially tuned to identify ESXi hosts by terminating all virtual machines running on the compromised host before starting the encryption process. The exact original infected used to distribute the ransomware is currently unknown.
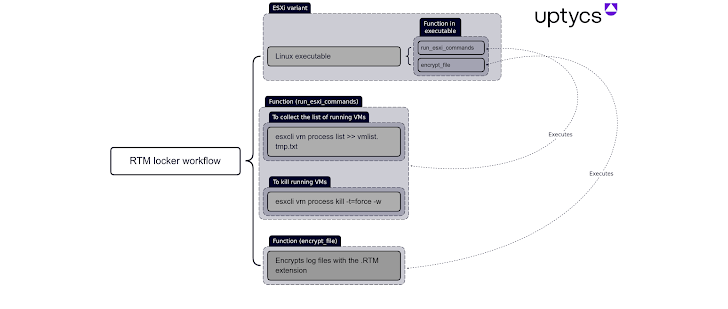
“It compiles and strips statically, making it more difficult to reverse engineer and allowing the binary to run on more systems,” explains Uptycs. “Crypto functions also use pthreads (aka POSIX threads) for faster execution.”
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
Save my seat!
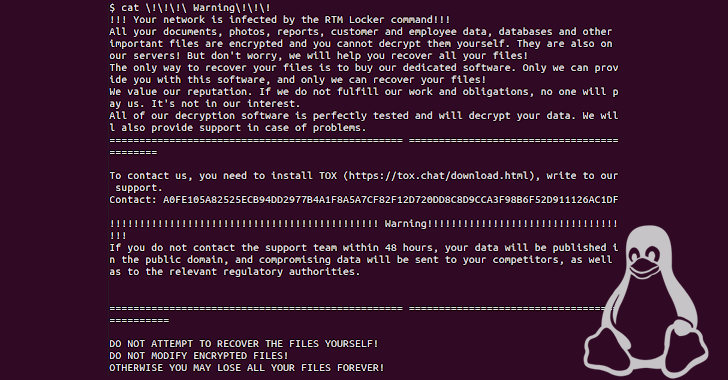
After successful encryption, victims are urged to contact their support team within 48 hours via Tox. Otherwise, you risk exposing your data. Decrypting a file locked with RTM Locker requires the public key appended to the end of the encrypted file and the attacker’s private key.
This development comes when Microsoft revealed that vulnerable PaperCut servers were being actively targeted by threat actors deploying Cl0p and LockBit ransomware.











