Behind a “malicious post” campaign on social media platforms that infected over 500,000 devices worldwide in the last three months to deliver variants of information stealers such as S1deload Stealer and SYS01stealer: Vietnamese attackers have been implicated.
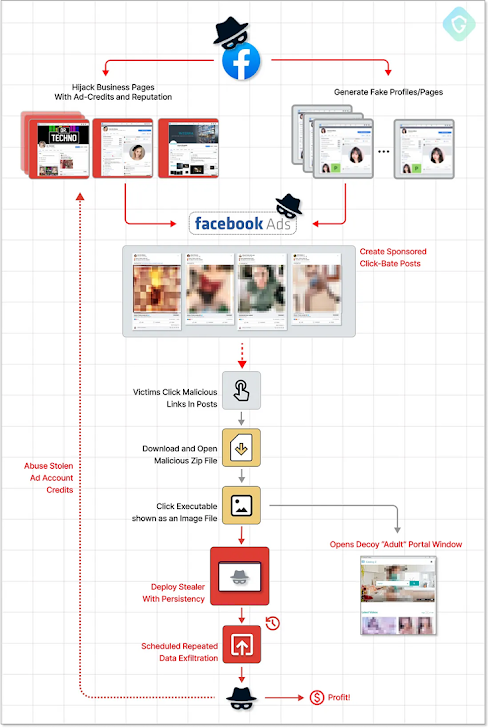
Malverposting is the mass dissemination of malicious software or other security threats using social media posts promoted on services such as Facebook and Twitter. The idea is to reach a wider audience by paying for ads to “amplify” your posts.
According to Guardio Labs, such attacks involve attackers creating new business profiles and hijacking already popular accounts to serve ads claiming free downloads of adult photo albums. starts with.

Inside these ZIP archive files are images that are actually executables that, when clicked, activate the infection chain, ultimately deploying the stealer malware, storing session cookies, account data, and more. information is collected.
The attack chain is highly effective, using information looted using stealers to create an ever-expanding army of hijacked Facebook bot accounts, which are then used to push sponsored posts. It is very effective as it creates a ‘vicious cycle’ where the .
To stay under Facebook’s radar, the threat actor was found to disguise newly generated business profile pages as photographer accounts. The majority of infections have been reported in Australia, Canada, India, the United Kingdom, and the United States.
The methods of deploying PHP-based stealers are said to be constantly evolving to incorporate more detection evasion features. This suggests that the threat actors behind the campaign are actively refining and restructuring their tactics in response to public information.
“Malicious payloads are highly sophisticated, constantly changing, and introducing new evasion techniques,” said Nati Tal, a security researcher at Guardio Labs.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
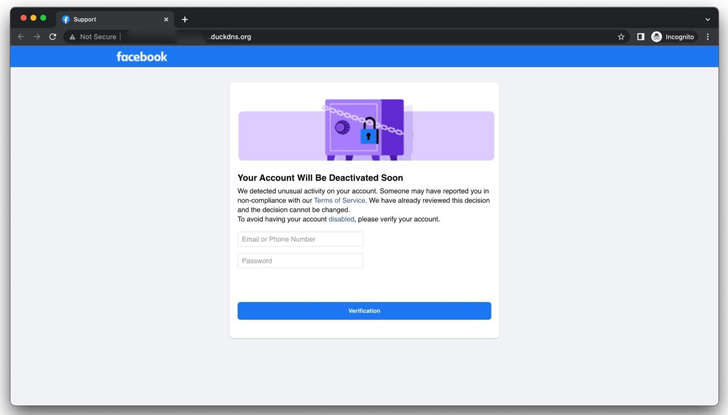
The findings indicate that Group-IB is currently targeting Facebook users by tricking them into entering their credentials into a fake copycat site designed to steal account credentials and hijack profiles. for revealing details of an ongoing phishing operation.
In a related development, Malwarebytes tricked users searching for games and cooking recipes on Google by serving malicious ads and redirecting them to fake websites made with Weebly to commit tech support scams. We have discovered a malvertising campaign intended to









