
Three new security flaws have been revealed in the Microsoft Azure API Management service. It can be exploited by malicious actors to access sensitive information and backend services.
According to Israeli cloud security firm Ermetic, this includes two server-side request forgery (SSRF) flaws and one instance of the unlimited file upload feature in the API Management developer portal.
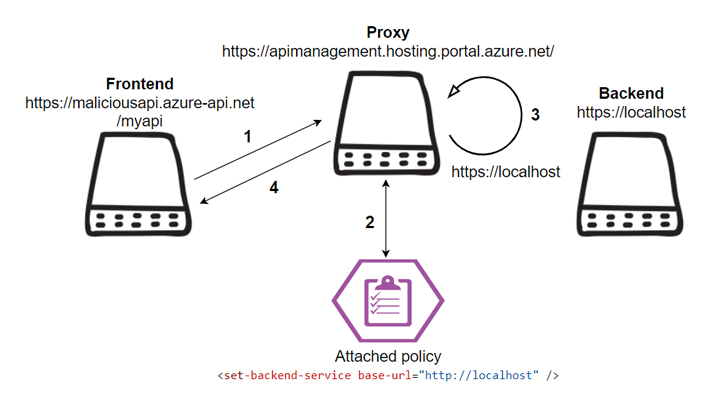
“By exploiting the SSRF vulnerability, an attacker could send requests from the service’s CORS proxy and the hosting proxy itself, access Azure’s internal assets, deny service, and bypass the web application’s firewall. You can,” said security researcher Liv Matan in a report shared with The Hacker News.
“File upload path traversal could allow an attacker to upload a malicious file to an Azure hosted internal workload.”
Azure API Management is a multi-cloud management platform that enables organizations to securely expose their APIs to external and internal customers, enabling a wide range of connected experiences.

One of the two SSRF flaws identified by Ermetic is a bypass of a patch introduced by Microsoft to address a similar vulnerability reported by Orca earlier this year. Another vulnerability exists in the API Management proxy functionality.
SSRF flaws can be exploited to compromise confidentiality and integrity, allowing threat actors to read internal Azure resources and execute unauthorized code.
On the other hand, a path traversal flaw found in the developer portal is caused by a lack of file type and path validation for uploaded files.
An authenticated user could use this loophole to upload a malicious file to the developer portal server and even execute arbitrary code on the underlying system.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
Following responsible disclosure, Microsoft patched all three flaws.
The findings come weeks after Orca researchers detailed a “design flaw” in Microsoft Azure that allowed attackers to gain access to storage accounts or move laterally within the environment. or even execute remote code.
It also follows the discovery of another Azure vulnerability called EmojiDeploy that could allow an attacker to take control of a targeted application.









