
Italian corporate banking customers have been targeted in an ongoing financial fraud campaign leveraging a new web-inject toolkit. Driven At least since 2019.
“The primary goal of the drIBAN fraud operation is to infect Windows workstations within a corporate environment to modify legitimate bank transfers made by victims by changing recipients and transferring funds to fraudulent bank accounts. ,” said Cleafy researchers Federico Valentini and Alessandro Strino.
According to an Italian cybersecurity firm, the bank accounts are controlled by the threat actors themselves or their affiliates, tasked with laundering the stolen funds.
Using web injects is a proven tactic that allows malware to inject custom scripts on the client side via man-in-the-browser (MitB) attacks to intercept traffic to and from the server.

Fraudulent transactions are often accomplished through a technology called an automated transfer system (ATS). ATS can bypass anti-fraud systems put in place by banks and initiate fraudulent wire transfers from the victim’s own computer.
Over the years, the operators behind drIBAN have become adept at evading detection and developing effective social engineering strategies, in addition to establishing a long-term foothold in corporate banking networks. I was.
Clafy said 2021 was the year that classic “banking Trojan” operations evolved into advanced and persistent threats. Additionally, there are indications that the activity cluster overlaps with his 2018 campaign launched by the attacker tracked by Proofpoint as his TA554 targeting users in Canada, Italy, and the UK. .
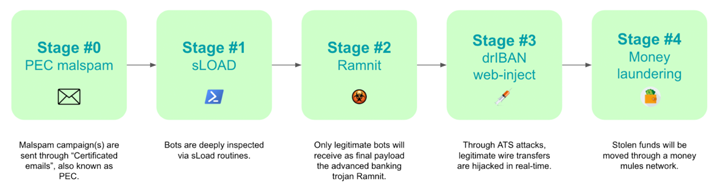
The attack chain begins with an authenticated email (or PEC email) that attempts to give the victim a false sense of security. These phishing emails contain an executable file that acts as a malware downloader called sLoad (aka Starslord loader).
The PowerShell loader, sLoad, is a reconnaissance tool that gathers and steals information from compromised hosts, assessing targets and dropping more important payloads such as Ramnit if the target is deemed beneficial. is intended for
“This ‘hardening phase’ could last for days or weeks, depending on the number of infected machines,” said Clafy. “Additional data is extracted to make the resulting botnet more robust and consistent.”
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
sLoad also leverages Living Off The Land (LotL) techniques by abusing legitimate Windows tools like PowerShell and BITSAdmin as part of its evasion mechanism.
Another feature of this malware is that it checks a predefined list of corporate financial institutions to determine if the hacked workstation is one of its targets, and if so, it attempts to infect. Function to continue.
“All bots that successfully pass these steps are selected by botnet operators to be considered ‘new candidates’ for bank fraud activity and proceed to the next stage. There, Ramnit, one of his most advanced banking Trojans, is installed. said the researcher.











