
Users of the Advanced Custom Fields plugin for WordPress are being asked to update to version 6.1.6 due to a security flaw discovered.
The issue, which has been assigned the identifier CVE-2023-30777, relates to a case of Reflected Cross-Site Scripting (XSS) that can be exploited to inject arbitrary executable script into innocent websites. increase.
Available in both free and pro versions, the plugin has over 2 million active installs. This issue he discovered on May 2nd, 2023 and was reported to the maintainer.
Patchstack researcher Rafie Muhammad said, “This vulnerability allows an unauthenticated user to steal sensitive information. In this case, a WordPress You can do privilege escalation on the site.”

Reflected XSS attacks typically occur when a victim is tricked into clicking a bogus link sent via email or another channel. This sends malicious code to a vulnerable website and the attack is reflected in the user’s browser.
This element of social engineering means that reflected XSS does not have the same scope and scale as stored XSS attacks, encouraging attackers to distribute malicious links to as many victims as possible. increase.
“[A reflected XSS attack] This is usually the result of insufficiently sanitized incoming requests, which can manipulate web application functionality and launch malicious scripts,” Imperva said.
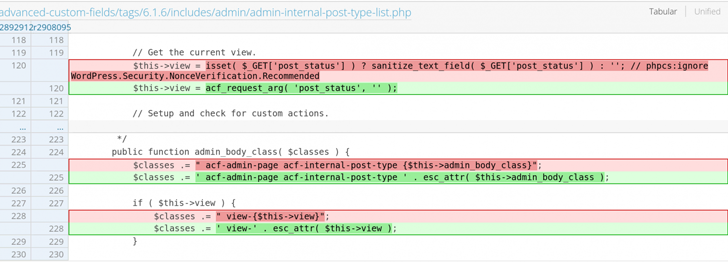
Note that CVE-2023-30777 can be activated with a default installation or configuration of Advanced Custom Fields. However, it is only possible from logged-in users who have access to the plugin.
This development is due to Craft CMS patching two moderate severity XSS flaws (CVE-2023-30177 and CVE-2023-31144) that threat actors have exploited to deliver malicious payloads. may provide.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
It could also be exploited without authentication to execute arbitrary JavaScript following the disclosure of another XSS flaw in the cPanel product (CVE-2023-29489, CVSS score: 6.1).
“Attackers can attack applications running on ports 80 and 443 as well as cPanel’s administrative ports,” said Assetnote’s Shubham Shah, adding that an adversary could hijack a valid user’s cPanel session. added that there is
“Acting on behalf of an authenticated user in cPanel, it’s usually trivial to upload a web shell and execute commands.”









