
Last month, the threat actor behind the ransomware attack against Taiwanese PC maker MSI leaked the company’s secret code-signing key on its dark website.
Alex Matrosov, founder and CEO of firmware security company Binarly, said: Said Weekend tweet.
“Intel Boot Guard may not be enabled on certain devices based on 11th Tiger Lake, 12th Adler Lake, and 13th Raptor Lake.”

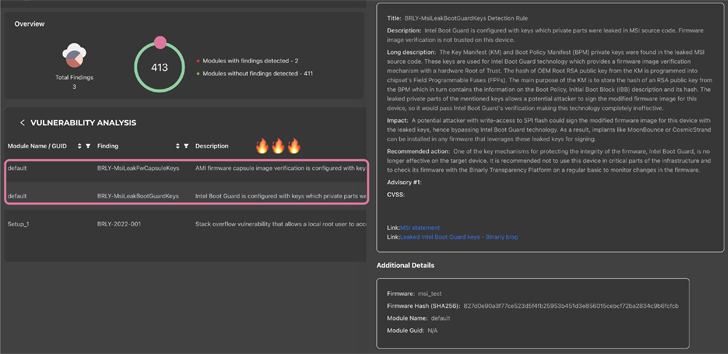
The exfiltrated data includes firmware image signing keys associated with 57 PCs and private signing keys for Intel Boot Guard used in 116 MSI products. MSI’s Boot Guard Key is believed to affect multiple device vendors including Intel, Lenovo, and Supermicro.
Intel Boot Guard is a hardware-based security technology designed to protect your computer from running modified UEFI firmware.
This development comes a month after MSI fell victim to a double extortion ransomware attack carried out by a new ransomware gang known as Money Message.
“The affected systems are gradually resuming normal operations, and there is no significant impact on financial business,” MSI said in a regulatory filing at the time. However, users are urged to obtain firmware/BIOS updates only from official websites and refrain from downloading files from other sources.
Leaked keys pose a significant risk as attackers can use them to sign malicious updates and other payloads and deploy them to targeted systems without raising any red flags.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
We have also followed another advisory from MSI advising users to be aware of fraudulent emails targeting the online gaming community.
This isn’t the first time UEFI firmware code has entered the public domain. In October 2022, Intel acknowledged a third party leak of Alder Lake BIOS source code. This also contained the private signing key used for Boot Guard.









