A cybersecurity researcher shares details about a security flaw currently being patched in the Windows MSHTML platform.
This vulnerability is tracked as CVE-2023-29324 (CVSS score: 6.5) and described as a security feature bypass. This has been addressed by Microsoft as part of the May 2023 Monthly Patch Update.
Akamai security researcher Ben Barnea, who found and reported the bug, said all versions of Windows are affected, but Microsoft, Exchange,
Servers with the March update omit the vulnerable functionality.

“An unauthenticated Internet attacker could use this vulnerability to force an Outlook client to connect to an attacker-controlled server,” Barnea shared with The Hacker News. said in a report.
“This introduces NTLM credential theft. This is a zero-click vulnerability, meaning it can be triggered without user interaction.”
It’s also worth noting that CVE-2023-29324 is a bypass of the hotfix introduced by Microsoft to resolve CVE-2023-23397 in March 2023. Attacks targeting European companies from April 2022 onwards.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
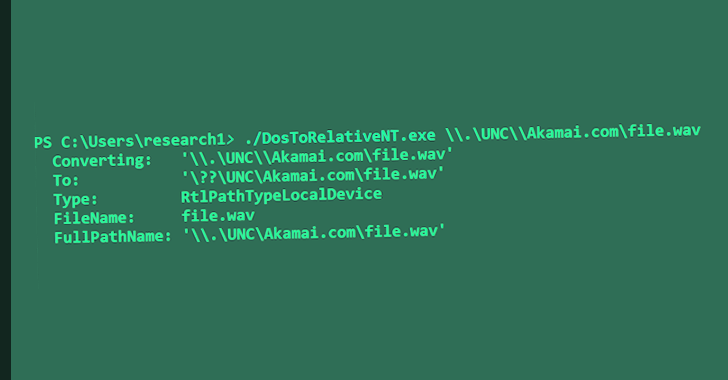
According to Akamai, the issue stems from complex handling of paths in Windows, which allows attackers to craft malicious URLs that can bypass Internet security zone checks.
“This vulnerability is an example of scrutiny of patches that lead to new vulnerabilities and bypasses,” Barnea said. “This is a zero-click media parsing attack surface and may contain severe memory corruption vulnerabilities.”
Microsoft further recommends that users install the Internet Explorer Cumulative Update that addresses vulnerabilities in the MSHTML platform and scripting engine to maintain full protection.











