
A so far undocumented and mostly undetected Linux backdoor variant called BPF door Cybersecurity firm Deep Instinct said in a technical report released this week that the virus has been found in the wild.
“BPFDoor maintains its reputation as a highly stealthy and difficult-to-detect malware in this version,” said security researchers Shor Virukomir Preisman and Eliran Nissan.
BPFDoor (aka JustForFun), first documented by PwC and Elastic Security Labs in May 2022, is a passive Linux backdoor associated with a Chinese threat actor called Red Menshen (aka DecisiveArchitect or Red Dev 18), which has become a global threat. It is known to pick out telecom providers in Middle East and Asia from at least 2021 onwards.
The malware is specifically aimed at establishing long-term, persistent remote access to compromised target environments, and evidence suggests hacking teams have been operating backdoors for years without detection. there is.

BPFDoor derives its name from its use of Berkeley Packet Filters (BPF), a technology that allows Linux systems to analyze and filter network traffic, to handle network communication and incoming commands.
By doing so, an attacker can enter a victim’s system and execute arbitrary code without being detected by the firewall, while filtering out unwanted data.
Deep Instinct’s findings came from a BPFDoor artifact uploaded to VirusTotal on February 8, 2023. At the time of writing, he is the only three security vendors to flag ELF binaries as malicious.
One of the main features that makes the new version of BPFDoor even more evasive is that many hard-coded indicators have been removed and replaced with a static library (libtomcrypt) for encryption and command and control (C2) communication. It has a built-in reverse shell.
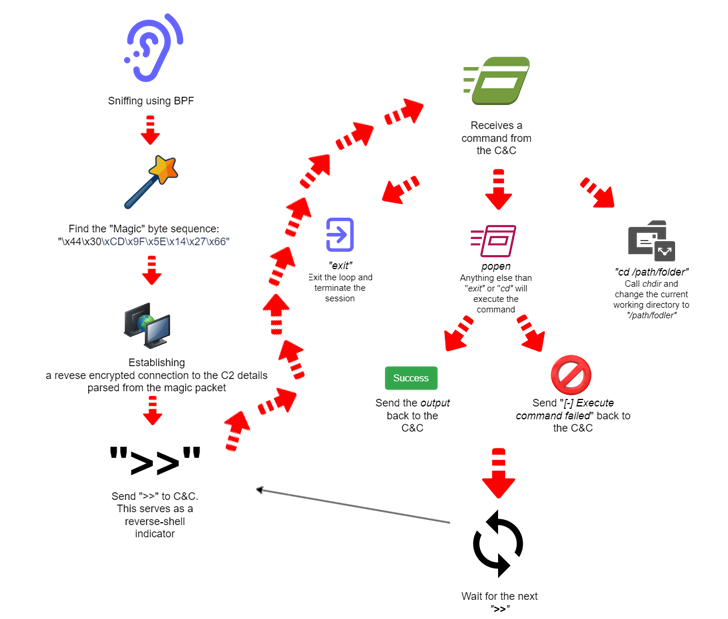
BPFDoor is configured on startup to ignore various operating system signals to prevent it from exiting. Next, by allocating a memory buffer and hooking a BPF filter onto the raw socket, we create a special packet-sniffing socket that monitors incoming traffic with specific magic byte sequences.
“When BPFdoor finds a packet with magic bytes in filtered traffic, it treats it as a message from an operator, parses the two fields and forks itself again,” the researchers explained.
“The parent process continues to monitor filtered traffic passing through the socket, while the child process treats the previously parsed fields as a command and control IP port combination and attempts to connect to it .”
Learn how to stop ransomware with real-time protection
Join our webinar to learn how to stop ransomware attacks using real-time MFA and service account protection.
Reserve your seat!
In the final stage, BPFDoor sets up an encrypted reverse shell session with its C2 server and waits for further instructions to be executed on the compromised machine.
The fact that BPFDoor has been kept under wraps for so long speaks to its sophistication, but its prevalence in enterprise and cloud environments has increased threat actors developing malware targeting Linux systems. .
This development saw Google announce a new enhanced Berkeley Packet Filter (eBPF) fuzzing framework called Buzzer to harden the Linux kernel and ensure that sandboxed programs running in privileged contexts are valid and safe. It was done in response to what was done.
The tech giant also said its testing methodology uncovered a security flaw (CVE-2023-2163) that could be exploited to achieve arbitrary reads and writes to kernel memory.









