of raspberry robin The worm has been used to attack telecommunications and government systems in Latin America, Australia, and Europe since at least September 2022.
“The main payload itself is packed with more than 10 layers of obfuscation, sandboxing and security analysis tools,” Trend Micro researcher Christopher Thor said in a technical analysis published Tuesday. can deliver bogus payloads.
The majority of infections were detected in Argentina, followed by Australia, Mexico, Croatia, Italy, Brazil, France, India and Colombia.
Due to the activity cluster Microsoft is tracking as DEV-0856, Raspberry Robin is increasingly being used by multiple actors as an initial access mechanism to deliver payloads such as the LockBit and Clop ransomware.
This malware is known to use infected USB drives as a distribution vector to download malicious MSI installer files. The MSI installer file deploys the main payload that facilitates post-exploitation.
Further analysis of Raspberry Robin reveals that heavy obfuscation is used to prevent analysis, as the malware “consists of two payloads embedded in a six-fold packed payload loader.” I was.
The payload loader is tuned to load a decoy payload, an adware called BrowserAssistant, which defeats detection efforts.
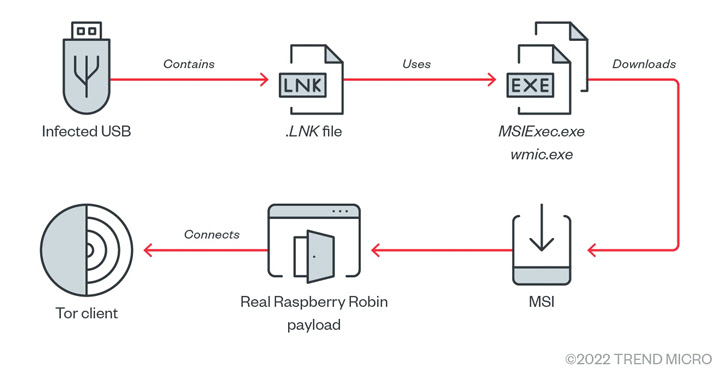
If no sandboxing and analysis is observed, it installs a legitimate payload and uses a custom TOR client embedded within it to connect to a hardcoded .onion address and wait for further commands.
The TOR client process masquerades as legitimate Windows processes such as dllhost.exe, regsvr32.exe, and rundll32.exe, again highlighting the great efforts threat actors are making to stay under the radar. .
Additionally, the actual routine of the malware runs in session 0. Session 0 is a special Windows session reserved for services and other non-interactive user applications to mitigate security risks such as smashing attacks.
Trend Micro said it found similarities in the privilege escalation and anti-debugging techniques used by Raspberry Robin and LockBit ransomware, suggesting a potential link between the two criminals.
“The group behind Raspberry Robin is the makers of some of the tools LockBit also uses,” speculates the company, instead “using the services of affiliates responsible for the technology LockBit uses. ‘ added.
That said, with no data returned from the TOR domain, the intrusion appears to be a reconnaissance operation, suggesting that the group behind the malware is “testing the waters to see how far its deployment will go.” suggests.









