
attacker behind Kingsing Cryptojacking operations have been discovered to exploit poorly configured and publicly available PostgreSQL servers to gain initial access to Kubernetes environments.
Microsoft Defender for Cloud security researcher Sunders Bruskin said in a report last week that the second initial access vector technique involves using a vulnerable image.
Kinsing has a history of targeting containerized environments. They often take advantage of misconfigured open Docker daemon API ports or abuse newly disclosed exploits to drop cryptocurrency mining software.
Attackers have also been found to use rootkits in the past to hide their presence and terminate and uninstall competing resource-intensive services and processes.
Now, according to Microsoft, the Kinsing attackers used a misconfiguration of the PostgreSQL server to gain their initial foothold, and the company has observed “massive clusters” infected in this manner.
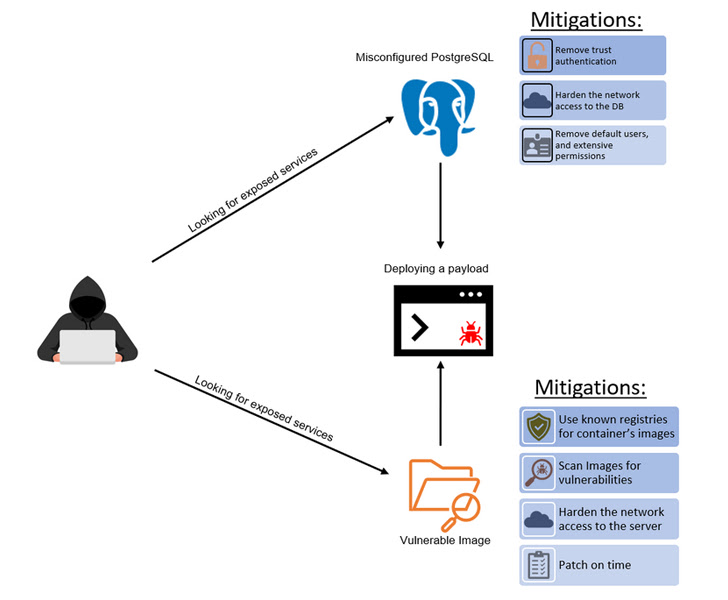
The misconfiguration is related to trust authentication settings and can be exploited to connect to a server without any authentication and achieve code execution if the option is set to accept connections from any IP address. may occur.
“In general, allowing access to a wide range of IP addresses exposes the PostgreSQL container to potential threats,” Bruskin explains.
Another attack vector targets servers with vulnerable versions of PHPUnit, Liferay, WebLogic, and WordPress, making them susceptible to remote code execution in order to execute malicious payloads.
Additionally, in a recent “widespread campaign”, the attackers scanned the open default WebLogic port 7001 and, if found, executed shell commands to launch malware.
“Exposing a cluster to the internet without proper security measures can expose it to attacks from external sources,” said Bruskin. “Additionally, attackers can use known vulnerabilities in the image to gain access to the cluster.”









