Governments and military organizations in the Asia-Pacific region are being targeted by a previously unknown Advanced Persistent Threat (APT) attacker, according to a new study.
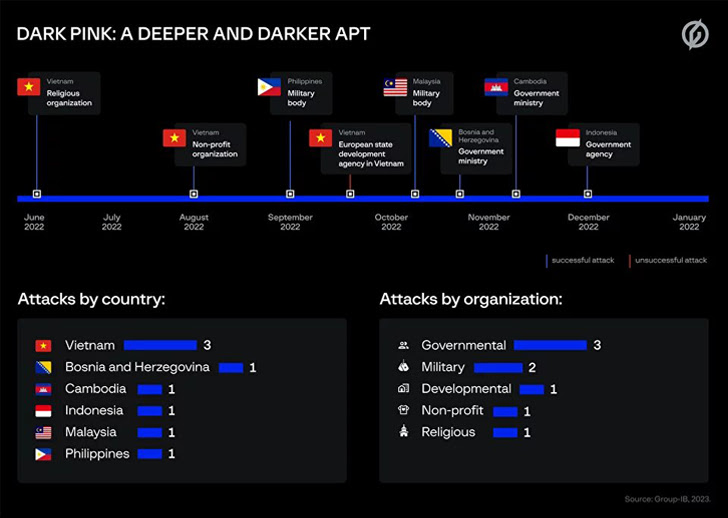
Group-IB, headquartered in Singapore, said in a report shared with The Hacker News that it tracks an ongoing campaign under the name: dark pink And, between June and December 2022, seven successful attacks were attributed to hostile groups.
Most of the attacks targeted military institutions, government ministries, religious groups and non-profit organizations in Cambodia, Indonesia, Malaysia, the Philippines, Vietnam and Bosnia and Herzegovina, with one unsuccessful intrusion into an unnamed European national development. is reported. Body based in Vietnam.
Estimated to be active in mid-2021, the threat actor has been active in just over a year with a never-before-seen custom toolkit designed to loot valuable information from compromised networks. Attacks spiked afterward.
“Dark Pink APT’s main purpose is to conduct corporate espionage, steal documents, capture audio from microphones of infected devices, and exfiltrate data from messengers,” said Group-IB researcher Andrey Polovinkin. described the operation as a “very complex APT campaign”. Initiated by a skilled attacker. ”
In addition to a sophisticated malware arsenal, this group has been observed leveraging spear phishing emails to launch attacks and leveraging the Telegram API for command and control (C2) communications. .
Also worth noting is the single GitHub account used to host the malicious module. The account has been active since May 2021, suggesting that Dark Pink has been operating undetected for his over a year and a half.
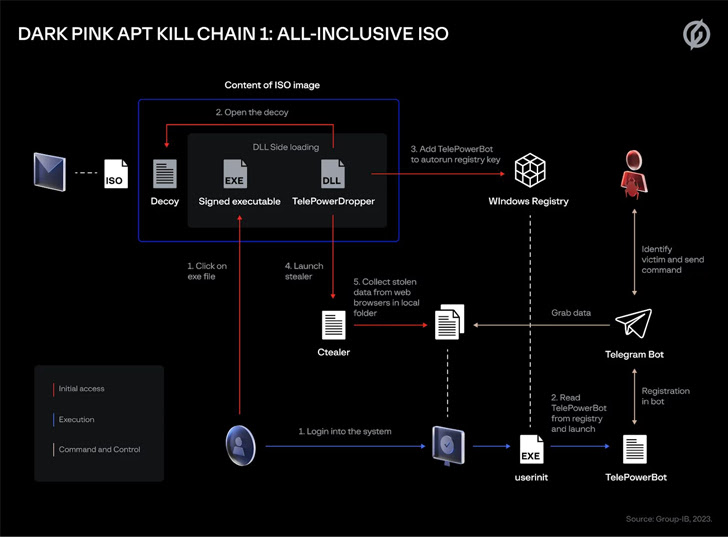
The Dark Pink campaign also stands out for employing multiple infection chains, with phishing messages containing links to booby-trapped ISO image files that launch the malware deployment process. In one instance, the attacker posed as a candidate applying for her PR internship.
It is also suspected that hacking crews may be trawling job boards in order to tailor messages and increase the likelihood of successful social engineering attacks.
The ultimate goal is to siphon credentials and cookies from web browsers using bespoke tools such as Ctealer and Cucky, as well as TelePowerBot and Telegram, which can execute commands sent via an attacker-controlled Telegram bot. Deploying KamiKakaBot.
Ctealer is written in C/C++, while Cucky is a .NET program. Another custom of his malware, ZMsg, is a .NET-based application that allows Dark Pink to collect messages sent via his Telegram, Viver, Zalo, and other messaging apps.
Another kill chain identified by Group-IB leverages decoy documents contained in ISO files to retrieve malicious macro-enablement templates from GitHub. This template contains TelePowerBot, a PowerShell script malware.
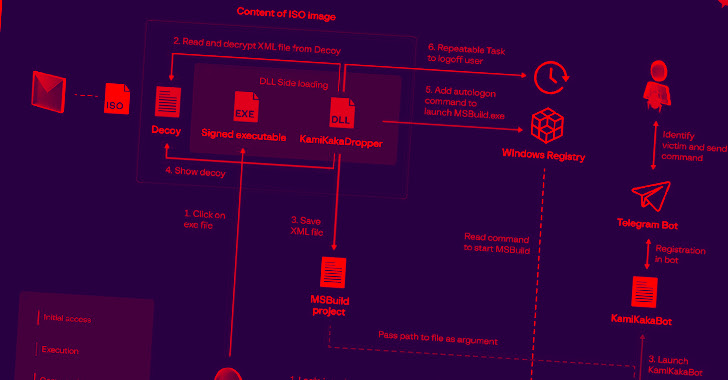
That’s not all. A third method, recently discovered in December 2022, invoked KamiKakaBot, a .NET version of TelePowerBot, with an XML file containing his MSBuild project at the end of a Word document in an encrypted view. will be Word files are included in ISO images sent to victims in spear-phishing emails.
“The threat actors behind this series of attacks were able to write tools in several programming languages, giving them flexibility when attempting to compromise defense infrastructure and infiltrate victim networks. ‘, explains Polovinkin.
After a successful intrusion, reconnaissance, lateral movement, and data exfiltration activities take place, with the attacker sometimes using Dropbox and email to send the desired files. He also uses his publicly available PowerSploit module to record microphone audio on the device and execute commands to infect connected USB disks to spread malware.
“The use of almost entirely custom toolkits, sophisticated evasion techniques, the ability of threat actors to rework malware to ensure maximum effectiveness, and the profile of targeted organizations make this particular group It shows the threat it poses,” said Polovinkin.









