
A recent IcedID malware attack allowed the attacker to compromise an unnamed target’s Active Directory domain within 24 hours of gaining initial access.
In a report published this week, Cybereason researchers said, “Throughout the attack, attackers used reconnaissance commands, credential theft, lateral movement through Windows protocol exploitation, and Cobalt Strike on newly compromised hosts. I was following the routine of running the
IcedID, also known as BokBot, began life as a banking Trojan in 2017 before evolving into a dropper for other malware, joining Emotet, TrickBot, Qakbot, Bumblebee, Raspberry Robin, and others.
Attacks related to IcedID delivery use a variety of methods, especially following Microsoft’s decision to block macros from Office files downloaded from the web.
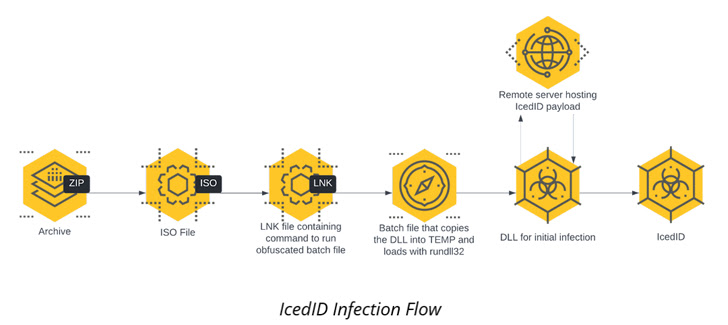
The intrusion detailed by Cybereason is no different in that the infection chain begins with an ISO image file contained within a ZIP archive that culminates in the execution of the IcedID payload.
The malware then establishes persistence on the host via scheduled tasks and communicates with remote servers to download additional payloads. This includes Cobalt Strike Beacons for subsequent reconnaissance operations.
It also performs lateral movement across the network, running the same Cobalt Strike Beacon on all those workstations, and then installs a legitimate remote management tool, Atera Agent, as a redundant remote access mechanism.
“Using such IT tools, attackers can create additional ‘backdoors’ if the initial persistence mechanism is discovered and modified,” the researchers said. increase. “These tools are less likely to be detected by antivirus and EDR, and more likely to be dismissed as false positives.”
Cobalt Strike Beacon is also used as a conduit to download a C# tool called Rubeus to steal credentials, ultimately allowing the attacker to laterally navigate to a Windows Server with domain admin privileges.
Elevated permissions are weaponized to launch the DCSync attack, allowing an attacker to simulate the behavior of a domain controller (DC) and obtain credentials from other domain controllers.
Other tools used as part of the attack include a legitimate utility named netscan.exe that scans the network for lateral movement and uses the rclone file synchronization software to target directories. Steals to MEGA cloud storage service.
This finding comes as Team Cymru researchers shed more light on the BackConnect (BC) protocol used by IcedID to provide additional post-compromise functionality, such as a VNC module that provides a remote access channel. it was done.
“In the case of BC, two operators seem to manage the whole process in different roles,” the researchers noted last month, adding that “much of the activity […] Occurs on a typical weekday. “
This development follows a report from Proofpoint in November 2022 that a resurgence of Emotet activity was linked to the distribution of a new version of IcedID.









