An unidentified attacker has deployed a new backdoor that borrows functionality from the US Central Intelligence Agency (CIA) Hive multi-platform malware suite. The source code for this backdoor was published by WikiLeaks in November 2017.
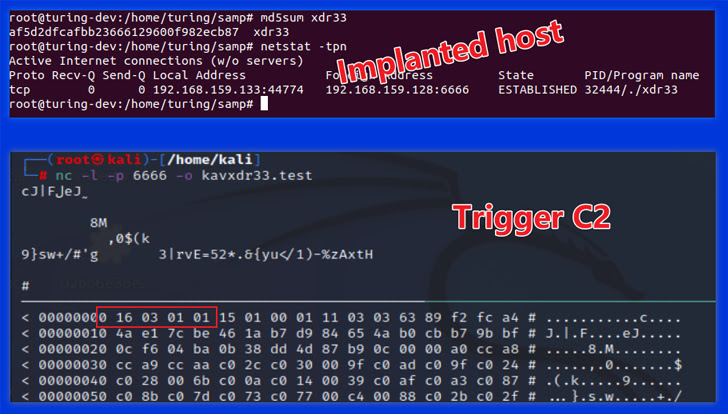
“This is the first time we actually found a variant of the CIA Hive attack kit, and we named it. xdr33 It is based on the embedded bot-side certificate CN=xdr33,” said Alex Turing and Hui Wang of Qihoo Netlab 360 in a technical article published last week.
xdr33 is said to spread by exploiting an unspecified N-day security vulnerability in F5 appliances. Uses SSL with forged Kaspersky certificates to communicate with command and control (C2) servers.
According to the Chinese cybersecurity firm, the purpose of the backdoor is to collect sensitive information and act as a starting point for subsequent intrusions. , improve Hive.
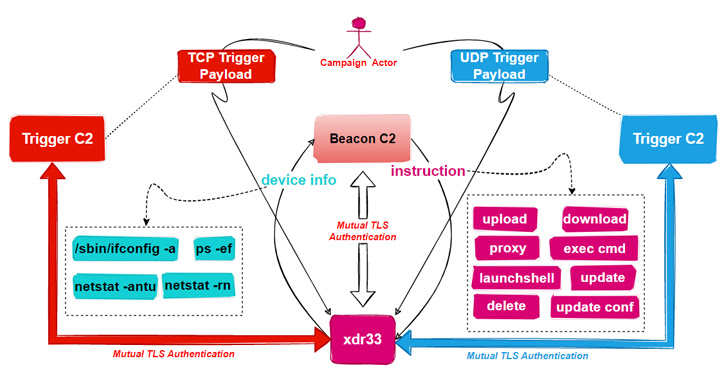
The ELF sample also acts as a beacon by periodically exfiltrating system metadata to remote servers and executing commands issued by the C2.

It has the ability to download and upload arbitrary files, execute commands using cmd, and launch shells, as well as update and clear traces of itself from compromised hosts. included.
The malware also incorporates a trigger module designed to sniff network traffic for specific “trigger” packets. This is to extract the C2 server mentioned in the payload of the IP packet, establish a connection and wait to execute commands sent by the C2.
“Please note that Trigger C2 has different communication details than Beacon C2. After establishing the SSL tunnel, [the] The bot and trigger C2 use a Diffie-Hellman key exchange to establish a shared key, which is then used with the AES algorithm to create a second layer of encryption,” the researchers explained.











