AI-Driven Ransomware FunkSec Targets 85 Victims Using Double Extortion Tactics
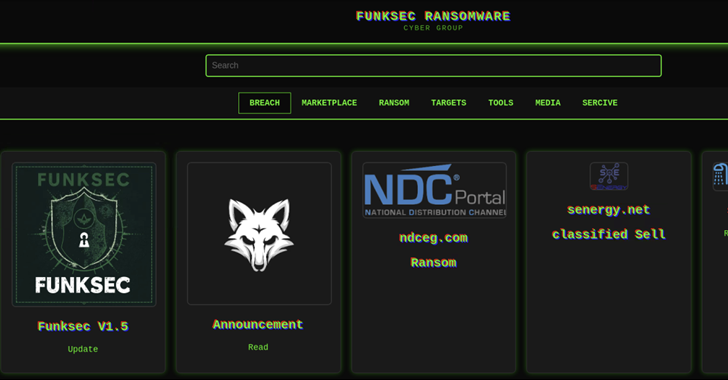
Cybersecurity researchers have shed light on a nascent artificial intelligence (AI) assisted ransomware family called FunkSec that sprang forth in late 2024, and has claimed more than 85 victims to date. “The group uses double extortion tactics, combining data theft…