Microsoft warned that malicious hackers were able to get the software giant to digitally sign their code, so it could be used for attacks such as deploying ransomware.
In an advisory published on Microsoft’s website coinciding with the release of its regular Patch Tuesday updates, Microsoft said that multiple cybercrime groups had exploited Microsoft’s Windows hardware developer program to deploy malware in the wild. I explained that I was able to get the driver to prove that. .
Malicious third-party drivers have been able to slip under the radar of many security services that implicitly trust anything digitally signed by Microsoft as trustworthy.
Once an attacker breaks into a Windows computer and gains administrator access, they can use signed drivers to disable security software and help spread the attack throughout the network.
Security researchers from various companies first alerted Microsoft to the issue in October, when Microsoft-signed Windows kernel driver code was deployed and used to spread attacks such as the Cuba ransomware. I understand.
This month, CISA and the FBI reported that Cuban ransomware extorted more than $60 million in ransoms.
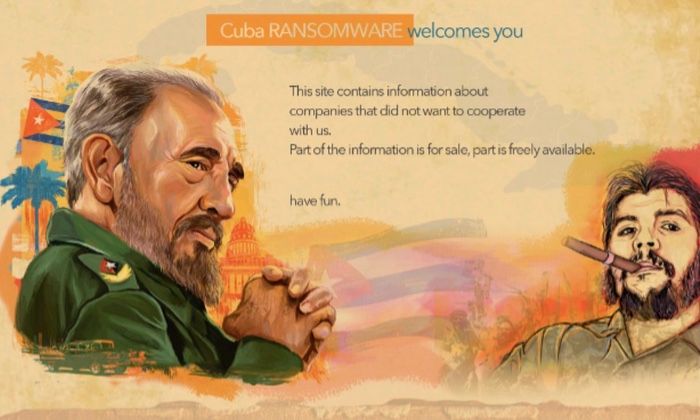
Cuba Ransomware, which is not believed to have any connection or affiliation with the country of Cuba, renames the encrypted files, giving them a “.cuba” file extension, and is used on websites. Displays Cuban-themed iconography in .
Microsoft is now revoking certificates and suspending developer accounts used to sign malicious drivers. Additionally, Microsoft recommends that all customers install the latest security updates and keep their antivirus defenses up to date.
Microsoft has found no evidence that its network has been compromised, and the extent of the attack (as far as it pertains to itself) is that it was tricked into signing drivers used in attacks against other organizations. is emphasized. .









