Users searching for popular software are being targeted in new malvertising campaigns that abuse Google ads to deliver trojanized variants that deploy malware such as Raccoon Stealer and Vidar. increase.
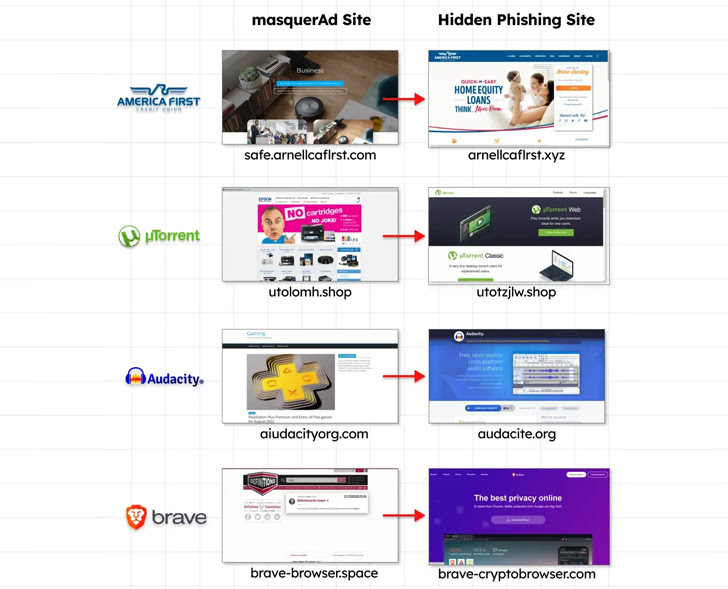
The campaign relies on seemingly trustworthy websites with typosquatted domain names that appear at the top of Google search results in the form of malicious ads by hijacking searches for specific keywords. increase.
The ultimate goal of such attacks is to trick unsuspecting users into downloading malicious or potentially unwanted applications.
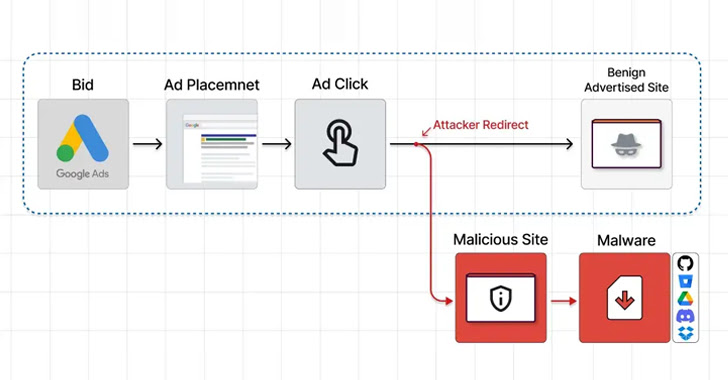
In one campaign published by Guardio Labs, we see attackers creating a network of benign sites that are being promoted on search engines. Clicking on these sites redirects visitors to a phishing page containing a trojanized ZIP archive of him hosted on Dropbox or OneDrive.
“The moment these ‘fake’ sites are visited by the targeted visitor (the one who actually clicked on the promoted search result), the server instantly redirects them to the malicious site, from which malicious ,” said researcher Nati Tal.

Camouflaged software includes AnyDesk, Dashlane, Grammarly, Malwarebytes, Microsoft Visual Studio, MSI Afterburner, Slack, and Zoom.
Guardio Labs, which dubbed the campaign MasquerAds, believes it came from a threat actor it tracks under the name Vermux, who “abuses a huge number of brands and continues to evolve.”
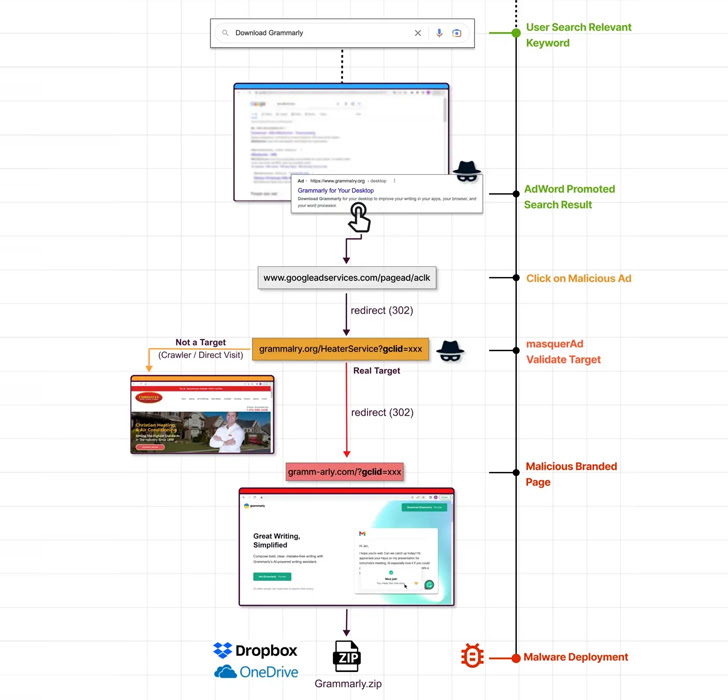
The Vermux operation singled out users primarily in Canada and the United States, using masquerAds sites tailored to search for AnyDesk and MSI Afterburner to proliferate cryptocurrency miners and Vidar information stealers.
This development demonstrates the continued use of typosquatted domains that mimic legitimate software to lure users into installing malicious Android and Windows apps.
It’s also not the first time the Google Ads platform has been used to deliver malware. Last month, Microsoft unveiled an attack campaign it uses to deploy his BATLOADER using advertising services to drop the Royal ransomware.
BATLOADER aside, malicious actors use malvertising techniques to distribute IcedID malware via clone web pages of well-known applications such as Adobe, Brave, Discord, LibreOffice, Mozilla Thunderbird, TeamViewer, and others.
Trend Micro said last week, “IcedID is a notable malware family that can deliver other payloads, including Cobalt Strike and other malware.” It can perform highly impactful follow-through attacks that lead to system-wide compromises.”
The findings of the study were published by the U.S. Federal Bureau of Investigation (FBI) as “malicious sites where cybercriminals use search engine advertising services to impersonate brands and host ransomware to steal login credentials and other financial information. It also came out when I warned that it is directing users to









