
Microsoft’s decision to block Visual Basic for Applications (VBA) macros by default in Office files downloaded from the Internet has prompted many attackers to improvise attack chains in recent months. rice field.
Today, according to Cisco Talos, Advanced Persistent Threat (APT) actors and commodity malware families are increasingly using Excel add-in (.XLL) files as their initial intrusion vector.
Weaponized Office documents delivered via spear-phishing emails and other social engineering attacks remain one of the most popular entry points for criminal groups seeking to execute malicious code.
These documents traditionally urged victims to enable macros that displayed seemingly harmless content, simply activating malware execution covertly in the background.
To combat this exploit, starting in July 2022, Windows makers enacted a significant change to block macros in Office files attached to email messages, effectively blocking a key attack vector.
While this lockdown only applies to newer versions of Access, Excel, PowerPoint, Visio, and Word, malicious actors are experimenting with alternative infection vectors to deploy malware.
It turns out that one such method is an XLL file. Microsoft describes it as “a type of dynamic link library (DLL) file that can only be opened by Excel.”
In an analysis published last week, Cisco Talos researcher Vanja Svajcer said, “XLL files can be emailed. You may be able to open the file without knowing that it may be corrupted.”
The cybersecurity firm said the attackers used a mix of native add-ins written in C++ and add-ins developed using a free tool called Excel-DNA. This phenomenon has seen a significant spike since mid-2021 and continues this year.
That said, the first publicly documented exploit of the XLL was in 2017, when the China-linked APT10 (aka Stone Panda) attacker used the technique to backtrack via process hollowing. It is said to have inserted the door payload into memory.
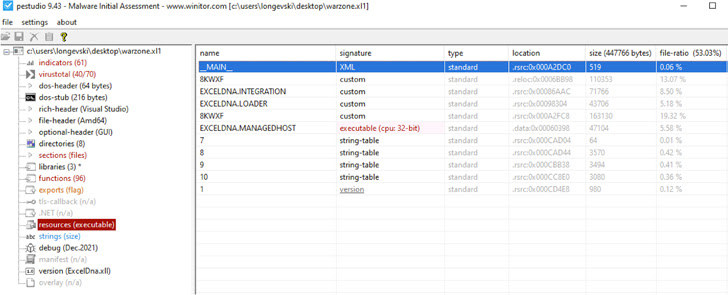
Since then, many other adversarial groups have followed in their footsteps, including TA410 (the attacker with links to APT10), DoNot Team, FIN7, and commodity malware families such as Agent Tesla, Arkei, Buer, Dridex, Ducktail, and Ekipa. is following RAT, FormBook, IcedID, Vidar Stealer, and Warzone RAT.
The exploitation of the XLL file format for distributing Agent Tesla and Dridex was previously highlighted by Palo Alto Networks Unit 42, noting that it “could represent a new trend in the threat landscape.” .
“As more and more users adopt new versions of Microsoft Office, attackers are turning away from VBA-based malicious documents to other formats such as XLL, or exploiting newly discovered vulnerabilities. can launch malicious code in the process space of Microsoft Office, an Office application,” Svajcer said.
Malicious Microsoft Publisher macro pushes Ekipa RAT
In addition to embedding an XLL Excel add-in, Ekipa RAT will receive an update in November 2022 to drop a remote access trojan leveraging Microsoft Publisher macros to steal sensitive information.
“Like other Microsoft Office products such as Excel and Word, Publisher files can contain macros that run when they are opened or closed. [of] This file presents an interesting initial attack vector from a threat actor’s perspective,” said Trustwave.
Note that Microsoft’s restriction preventing macros from running in files downloaded from the Internet does not apply to Publisher files, and attackers can abuse this method for phishing campaigns.
Trustwave researcher Wojciech Cieslak said: “The authors of this malware have tracked changes in the security industry, such as Microsoft blocking macros from the Internet, and have changed their tactics accordingly.”









