
Financial threat actors tracked as blind eagle has resurfaced with its sophisticated toolset and sophisticated infection chain as part of attacks targeting organizations in Colombia and Ecuador.
Check Point’s latest research provides new insights into the tactics and techniques of Spanish-speaking groups, including using advanced tools and government-themed lures to launch kill chains.
Also tracked under the name APT-C-36, Blind Eagle is noted for its narrow geographic focus and launching indiscriminate attacks against South American nations since at least 2018.
Blind Eagle’s activities were documented by Trend Micro in September 2021, revealing a spear-phishing campaign primarily targeting Colombian entities designed to deliver commodity malware known as BitRAT. , Ecuador, Spain, and Panama targets.
The attack chain begins with a phishing email containing a booby-trap link. Clicking on this link deploys an open source Trojan named Quasar RAT with the ultimate goal of accessing the victim’s bank account.
Banks targeted include Banco AV Villas, Banco Caja Social, Banco de Bogotá, Banco Popular, Bancoomeva, BBVA, Colpatria, Davivienda, and TransUnion.
If the recipient of the email is outside Colombia, the attack sequence will be aborted and the victim will be redirected to the official website of Migración Colombia, Colombia’s border control agency.
A related campaign that names both Colombia and Ecuador impersonates the latter’s Internal Revenue Service (SRI) and utilizes similar geoblocking techniques to filter out requests from other countries.
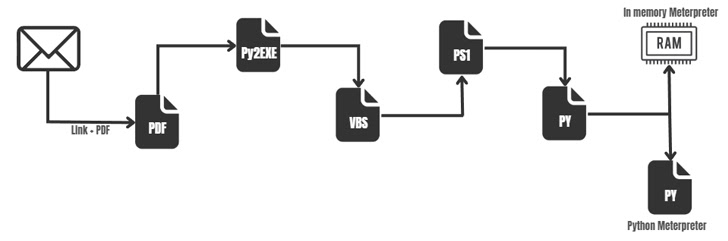
Rather than dropping the RAT malware, this attack employed a more complex multi-step process, exploiting the legitimate mshta.exe binary to execute VBScript embedded within HTML files and eventually to Download two Python scripts.
The first of the two, ByAV2.py, is an in-memory loader designed to execute the Meterpreter payload in DLL form. mp.py is also her Meterpreter artifact, just programmed in Python, and the attacker may be using one of them as a redundant way to maintain backdoor access to the host. indicates that there is
“The Blind Eagle is one of the strangest birds in the APT group,” concludes the researchers. “Judging from its toolset and routine operations, it is clear that it is more interested in cybercrime and financial gain than espionage.”
The development comes days after Qualys revealed that an unknown actor was using personal information stolen from a Colombian cooperative bank to create phishing emails that led to the deployment of BitRAT.









