
DevOps platform CircleCI on Wednesday urged customers to rotate all secrets after an unspecified security incident.
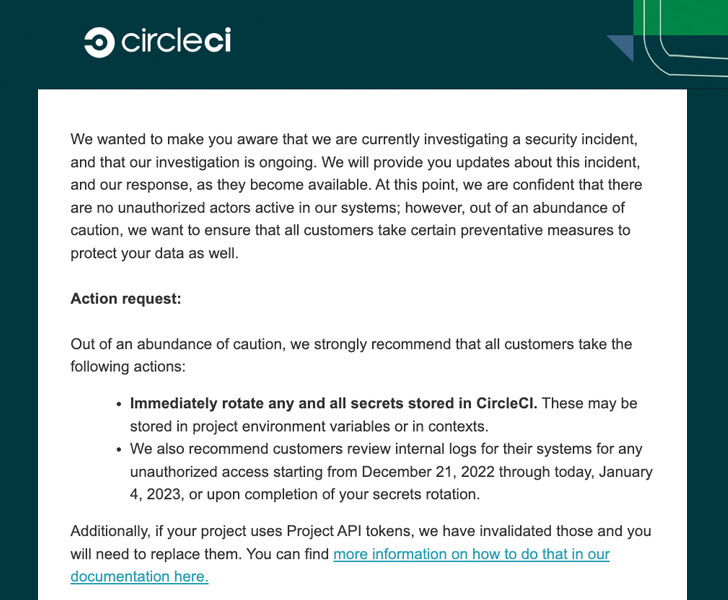
The company said an investigation was underway, but stressed that “there are no unauthorized actors active in our system.” Additional details will be shared in the coming days.
“Immediately rotate all secrets stored on CircleCI,” said Rob Zuber, CTO of CircleCI, in a succinct recommendation. “These may be stored in project environment variables or context.”
CircleCI also encourages users to review their internal logs for signs of compromised access between December 21, 2022 and January 4, 2023, or until the secret is rotated.
Software Development Services did not provide details about the breach, but said it has also disabled all project API tokens and should be replaced.
The disclosure comes a few weeks after the company announced that it had released a service reliability update on December 21, 2022, resolving an underlying “system issue.”
This is also the latest breach to hit CircleCI in recent years. The company said in September 2019 that he disclosed “unusual activity” involving a third-party analytics vendor that led to unauthorized access to usernames and email addresses associated with GitHub and Bitbucket.
And last year, it warned users that fake CircleCI email notifications were being used to steal GitHub credentials and two-factor authentication (2FA) codes.
Slack’s GitHub code repository stolen
As Slack disclosed on December 31, 2022, CircleCI was not made aware of the security issue involving unauthorized access to a subset of source code repositories on GitHub.
Uncovered on December 29, 2022, the issue stole a limited number of Slack employee tokens, which were used to access GitHub repositories, ultimately allowing adversaries to download the source code. Now
However, Slack said no customer action was required and the breach was quickly contained. After that the credentials are no longer valid.
“The downloaded repository did not contain customer data, any means of accessing customer data, or Slack’s core codebase,” the Salesforce-owned company said. “The threat actor did not have access to other areas of the Slack environment, including the production environment, nor did he have access to other of his Slack resources or customer data.”
The instant messaging service did not share further information about how the employee’s tokens were stolen, but “the unauthorized access was not due to a vulnerability specific to Slack.” emphasized.









