a notorious information thief known as further away continues to leverage popular social media services such as TikTok, Telegram, Steam, and Mastodon as intermediate command and control (C2) servers.
“When a user creates an account on the online platform, it generates a unique account page that anyone can access,” the AhnLab Security Emergency Response Center (ASEC) revealed in a technical analysis published late last month. “The attacker writes identifying characters and her C2 address on part of this page.”
In other words, this technique relies on disposable actor-controlled accounts created on social media to obtain C2 addresses.
The advantage of this approach is that if the C2 server is down or blocked, an attacker can easily set up a new server and edit the account page to allow previously distributed malware to communicate with the server. It is possible to circumvent the restrictions on
First seen in 2018, Vidar is a commercial malware capable of gathering various information from compromised hosts. It usually relies on delivery mechanisms such as phishing emails or cracked software to propagate.
“Once information gathering is complete, the extorted information is compressed into a ZIP file, encoded in Base64 and sent to the C2 server,” said the ASEC researchers.
A new feature in the latest version of the malware (version 56.1) is that the collected data is encoded before extraction. This is a change from previous variants known to send compressed file data in plaintext format.
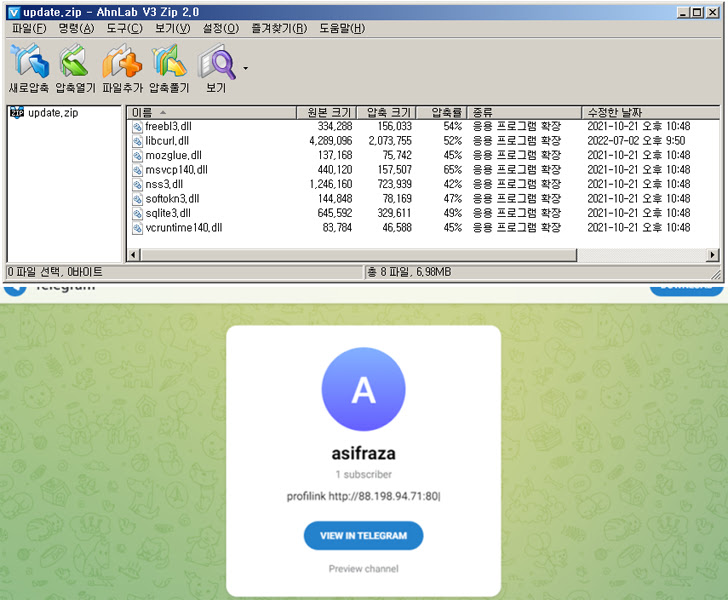
“Vidar uses a well-known platform as an intermediate C2, so it has a long lifespan,” said the researchers. “The attacker’s account, created six months ago, is still maintained and continuously updated.”
This development comes amid recent discoveries that malware is being distributed using a variety of methods. This includes malicious Google ads and a malware loader called Bumblebee. Bumblebee is by threat actors tracked as Exotic Lily and Projector Libra.
Risk consulting firm Kroll said it found ads for the GIMP open source image editor in an analysis published last month. Clicking on this ad redirects the victim to a typosquatted domain hosting his Vidar malware.
If anything, the evolution of malware delivery methods in the threat landscape is part of a response to Microsoft’s decision to block macros by default in Office files downloaded from the internet after July 2022.
This has led to an increase in email attachments exploiting alternative file formats such as ISO, VHD, SVG, and XLL to bypass Mark of the Web (MotW) protections and evade anti-malware scanning measures. increase.
“Disc image files can bypass the MotW feature, because MotW is not inherited by files within the disc image file when they are extracted or mounted,” said the ASEC researcher, adding that HTML smuggling and VHD Malware using a combination of files.











