
A South African-based threat actor known as Automated Libra has been observed using CAPTCHA bypass techniques to programmatically create GitHub accounts as part of a freejacking campaign called PURPLEURCHIN.
William Gamazo and Nathaniel Quist, researchers in Unit 42 at Palo Alto Networks, said, “The group primarily targets cloud platforms that offer limited-time trials of cloud resources to perform cryptocurrency mining operations. “There are.”
PURPLEURCHIN was first revealed in October 2022, when Sysdig revealed that the attackers created 30 GitHub accounts, 2,000 Heroku accounts, and 900 Buddy accounts to scale their operations.
According to Unit 42, this cloud threat actor group created 3-5 GitHub accounts every minute during peak activity in November 2022, with over 130,000 total fake accounts across Heroku, Togglebox, and GitHub. has been set.
It is estimated that over 22,000 GitHub accounts were created between September and November 2022, with 3 in September, 1,652 in October, and 20,725 in November. A total of 100,723 unique Heroku accounts were also identified.
Cybersecurity firms have also used cloud resources to exploit “play and run” systems designed to avoid paying platform vendor bills by utilizing counterfeit or stolen credit cards to create premium accounts. ” called tactics.
After analyzing 250GB of data, we saw the first signs of a cryptocurrency campaign at least 3.5 years ago in August 2019, identifying over 40 wallets and the use of seven different cryptocurrencies.
The core idea behind PURPLEURCHIN is to leverage the computational resources allocated to free and premium accounts of cloud services for massive financial gains before losing access due to non-payment of membership fees.
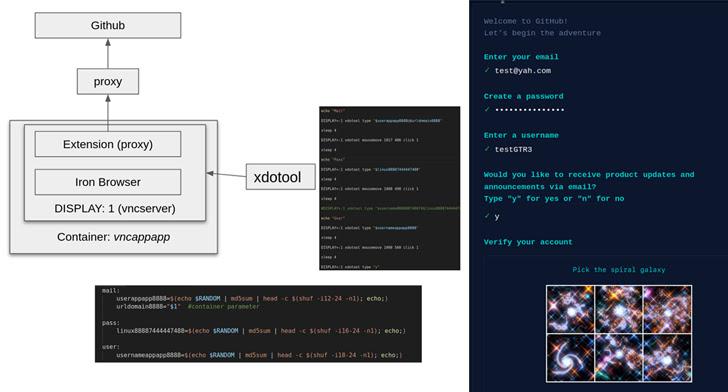
In addition to leveraging legitimate tools such as xdotool and ImageMagick to automate the account creation process, attackers have also been found to take advantage of vulnerabilities within GitHub’s CAPTCHA checks to facilitate illicit purposes. .

This is accomplished by using ImageMagick’s convert command to convert the CAPTCHA image to its RGB complement, then using the identify command to extract the skewness of the red channel and select the minimum value.
After successful account creation, Automated Libra will proceed to create a GitHub repository and deploy a workflow that will allow you to launch an external Bash script and container to start the cryptocurrency mining function.
The findings show how these platforms can weaponize freejack campaigns to maximize revenue by increasing the number of accounts that can be created per minute.
“It is important to note that Automated Libra has designed its infrastructure to take full advantage of CD/CI tools,” the researchers concluded.
“This has become easier to achieve over time as traditional VSPs diversify their service portfolios to include cloud-related services. It’s easier for attackers because they don’t need it to deploy the application.”











