Attackers published another round of malicious packages on the Python Package Index (PyPI) with the goal of delivering information-stealing malware to compromised developer machines.
Interestingly, the malware goes by many names, including ANGEL Stealer, Celestial Stealer, Fade Stealer, Leaf $tealer, PURE Stealer, Satan Stealer, and @skid Stealer, but cybersecurity firm Phylum claims they are all named Discovered to be a copy of W4SP Stealer.
W4SP Stealer primarily works by siphoning user data including credentials, cryptocurrency wallets, Discord tokens, and other files of interest. It is created and published by actors working under the aliases BillyV3, BillyTheGoat, and billythegoat356.
“For some reason, each deployment appears to simply attempt to find/replace W4SP references in exchange for seemingly arbitrary names,” the researchers said in a report published earlier this week.
The 16 malicious modules are modulesecurity, informmodule, chazz, randomtime, proxygeneratorbil, easycordey, easycordeyy, tomproxies, sys-ej, py4sync, infosys, sysuptoer, nowsys, upamonkws, captchaboy, proxybooster.
The campaign distributing the W4SP Stealer gained momentum around October 2022, but indicates it may have started as far back as August 25, 2022. Since then, dozens of additional fake packages, including W4SP Stealer, have been published on his PyPI by the persistent attacker.
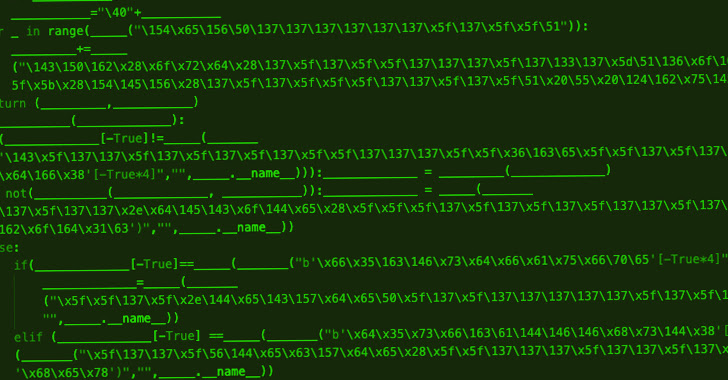
The latest iteration of the activity, for what it’s worth, apparently hides its malice, except in the case of chazz, which utilizes a package to download an obfuscated Leaf $tealer malware hosted at klgrth. is not.[.]I serve pasta.
It’s worth noting that previous versions of the attack chain have also been seen fetching the next-stage Python code directly from public GitHub repositories and dropping credential stealers.
The surge in new copycat variants coincided with GitHub’s removal of the repository that held the original W4SP Stealer source code, and cybercriminals likely not involved in this operation also released the malware. It shows that you are weaponizing and attacking PyPI users.
“Open source ecosystems such as PyPI and NPM are very easy targets for these types of attackers to deploy this type of malware,” said the researchers. Their attempts will be more frequent, more persistent and the most sophisticated. “
A software supply chain security firm monitoring the threat actor’s Discord channel further noted that a package previously flagged under the name pystyle was trojanized by BillyTheGoat to distribute the stealer. .
Not only did the module garner thousands of downloads each month, but it launched in September 2021 as a harmless utility to help users style their console output. A malicious change was introduced in versions 2.1 and 2.2 released on October 28, 2022.
These two versions had been available on PyPI for about an hour before being pulled, and were said to have been downloaded 400 times, BillyTheGoat told Phylum in an “unsolicited communication.” . The latest version available in the repository is 2.9.
“Just because a package is harmless today and shows a history of being harmless over the years doesn’t mean it will stay that way,” the researchers warned. They have shown great patience in creating a legitimate package, but poisoned it with malware after it became sufficiently popular.”











