Multiple High Severity Vulnerabilities Disclosed password status A password management solution that can be exploited by an unauthenticated, remote adversary to obtain a user’s plaintext password.
“A successful exploit could allow an unauthenticated attacker to steal passwords from the instance, overwrite all passwords stored in the database, or elevate privileges within the application.” , Swiss cybersecurity firm modzero AG said in a report published this week.
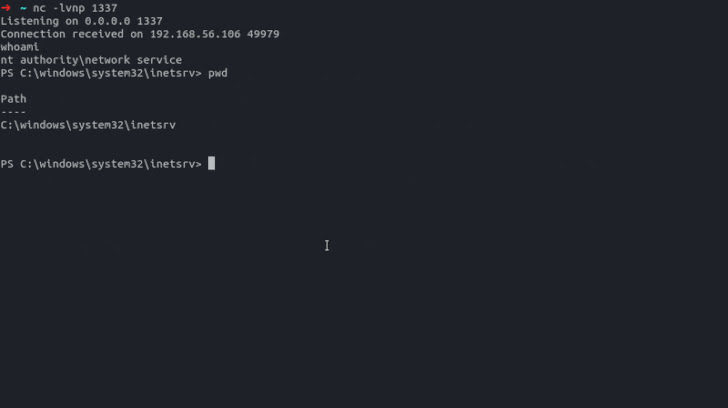
“Several of the individual vulnerabilities can be chained together to get a shell on the Passwordstate host system and dump all stored passwords in cleartext, starting with just valid usernames.”
Developed by an Australian company called Click Studios, Passwordstate has over 29,000 customers and is used by over 370,000 IT professionals.
One of the flaws also affects Passwordstate version 9.5.8.4 of the Chrome web browser. The latest version of the browser add-on is 9.6.1.2, released on September 7, 2022.
The list of vulnerabilities identified by modzero AG is as follows –
- CVE-2022-3875 (CVSS score: 9.1) – Passwordstate API authentication bypass
- CVE-2022-3876 (CVSS score: 6.5) – access control bypass with user-controlled keys
- CVE-2022-3877 (CVSS score: 5.7) – Cross-site scripting (XSS) vulnerability stored in the URL field of all password entries
- No CVE (CVSS score: 6.0) – Poor mechanism to protect passwords using server-side symmetric encryption
- No CVE (CVSS score: 5.3) – List audited events such as password requests and user account changes via API using hardcoded credentials
- No CVE (CVSS score: 4.3) – Use of insufficiently protected credentials against password lists
Exploiting the vulnerability could allow an attacker who knows the valid username to extract stored passwords in clear text, overwrite passwords in the database, and even execute code remotely with elevated privileges. I have.
Additionally, an improper authentication flow (CVSS score: 3.7) identified in the Chrome browser extension can be weaponized to send all passwords to attacker-controlled domains.
In the attack chain demonstrated by modzero AG, an attacker forged an API token for an admin account, exploited an XSS flaw to add a malicious password entry, obtained a reverse shell, and accessed an instance hosted on the may retrieve passwords that are
To mitigate potential threats, we recommend updating to Passwordstate 9.6 – Build 9653 released on November 7, 2022 or a later version.
In April 2021, Passwordstate fell victim to a supply chain attack that allowed attackers to leverage the service’s update mechanism to drop a backdoor onto customer machines.









