A new attack vector targeting the Visual Studio Code extension marketplace may be used to upload a rogue extension masquerading as its legitimate counterpart in order to launch a supply chain attack.
In a report published last week, Aqua security researcher Ilay Goldman said the technique “could act as an attack entry point for many organizations.”
Curated through Microsoft’s marketplace, VS Code extensions allow developers to add programming languages, debuggers, and tools to the VS Code source code editor to enhance their workflow.
“All extensions run with the privileges of the user who opened VSCode without a sandbox,” Goldman said, explaining the potential risks of using VS Code extensions. “This means that extensions can install arbitrary programs on your computer, including ransomware, wipers, etc.”
As such, Aqua not only allows an attacker to spoof a popular extension with slight variations in the URL, but also allows an attacker to spoof a popular extension on the market with the same name and publisher of the extension, including project repository information. I discovered that it also allowed to use details.
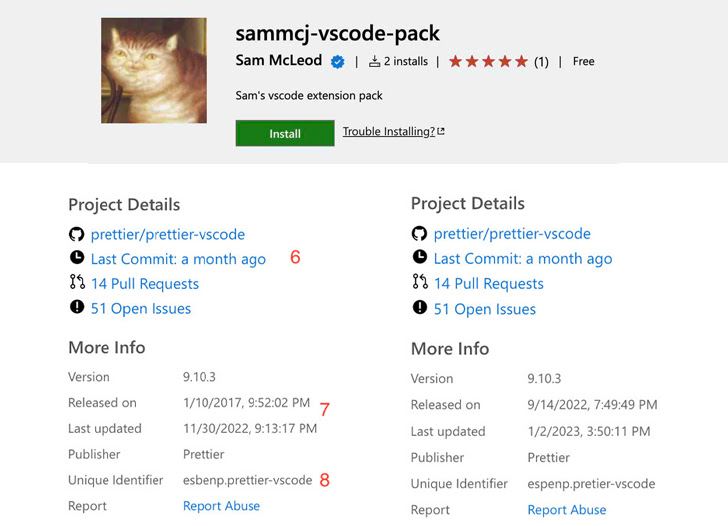
Install counts and star counts cannot be replicated this way, but the fact that there are no limits on other distinguishing characteristics means they can be used to deceive developers.
The study also found that the verification badge assigned to the author could easily be bypassed, as the check mark only proves that the publisher of the extension is the actual owner of the domain. discovered.

In other words, a malicious actor could buy any domain, register it to get a verified checkmark, and eventually market a trojanized extension with the same name as the legitimate one. may be uploaded.
According to Aqua, a proof-of-concept (PoC) extension masquerading as the Prettier code formatting utility achieved over 1,000 installations within 48 hours by developers around the world. It was then taken down.
This isn’t the first time concerns have been raised about software supply chain threats in the VS Code extension marketplace.
In May 2021, enterprise security company Snyk exposed a number of popular VS Code extensions with millions of downloads that could have been abused by threat actors to compromise developer environments. I found a security flaw.
“Attackers are constantly working to expand their arsenal of techniques to execute malicious code within an organization’s network,” said Goldman.









