A comprehensive analysis of the cryptographic protocols used by the Swiss encrypted messaging application Threema reveals a number of potential exploits to defeat authentication protections or recover users’ private keys. A loophole has been revealed.
According to ETH Zurich researchers Kenneth G. Paterson, Matteo Scarlata, and Kien Tuong Truong, who reported the issue to Threema on October 3, 2022, the seven attacks span three different threat models. From us dated November 29, 2022.
Threema is an encrypted messaging app with over 11 million users as of October 2022. “Security and privacy are deeply ingrained in his DNA at Threema,” the company claims on his website.
It is officially used by the Swiss government and the Swiss Army, and is also touted as a safe alternative alongside other services such as Signal, Meta-owned WhatsApp and Telegram.
Threema has undergone at least two third-party code audits (once in 2019 and twice in 2020), but the latest findings reveal issues in the application’s “cryptographic core”. was not enough to “
“Ideally, applications using new cryptographic protocols should come with their own formal security analysis (in the form of security proofs) to provide strong security guarantees,” the study said. said the person.
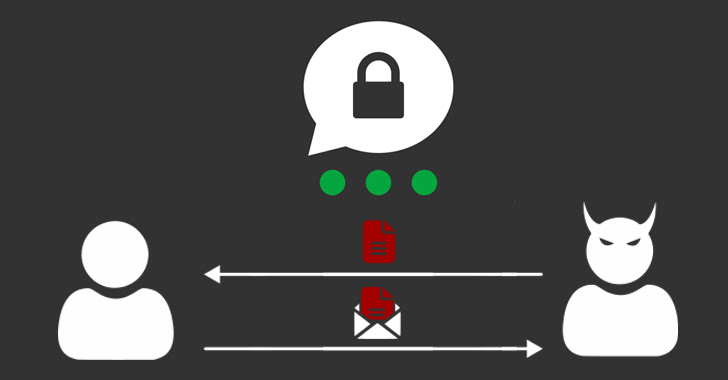
This allows an attacker to impersonate the client, rearrange the sequence of messages exchanged between the two parties, duplicate the victim user’s account, leverage backups, and more. A mechanism for recovering a user’s private key.
The latter two attack vectors, which require direct access to the victim’s device, can have serious consequences as they allow an adversary to surreptitiously access a user’s future messages without the user’s knowledge. there is.
We also uncovered instances of replay and reflection attacks involving Android apps that occurred when users reinstalled apps or changed devices, allowing malicious individuals to gain access to Threema servers. You will be able to play old messages. A similar replay attack was confirmed for him in January 2018.
Last but not least, adversaries launch the Kompromat attack, in which a malicious server tricks a client into “unwittingly encrypting a message selected by the server so that it can be delivered to another user.” can also do.
The attack was previously reported to Threema by Jonathan Krebs, a researcher at the University of Erlangen-Nuremberg, who released a fix (version 4.62 for Android and version 4.6.14 for iOS) in December 2021. It’s worth noting that I was prompted to ship.
“Using modern secure libraries for cryptographic primitives alone does not lead to secure protocol designs,” the researchers said. “Libraries such as NaCl and libsignal can be abused when building more complex protocols, and developers should be careful not to fall prey to a false sense of security.”
“The mantra ‘Don’t do your own cryptography’ is widely known today, but ‘Don’t write your own cryptographic protocol’ (assuming there already exists a protocol that meets the developer’s requirements). ),” they added. “For Threema, a bespoke he can replace the C2S protocol with TLS.”
When asked for comment, Threema told The Hacker News that it has released a new communication protocol. ibex This left “some of the issues obsolete,” he added, adding that “we acted immediately to implement a fix for all findings within a few weeks.”
“Some of the findings […] It may be interesting from a theoretical point of view, but none of it has had much of an impact in the real world.
Some attacks also rely on having physical access to an unlocked mobile device for an extended period of time, at which point “the entire device should be considered compromised.” points out.
The study arrives almost six months after ETH Zurich researchers detailed serious shortcomings of the MEGA cloud storage service. MEGA cloud storage services can be weaponized to crack private keys and completely compromise the privacy of uploaded files.
Then, in September 2022, another group of researchers revealed numerous security flaws in Matrix’s decentralized real-time communication protocol. This allows malicious server operators to read your messages or impersonate you, effectively compromising the confidentiality and trustworthiness of the service.









