A new malware campaign has been observed targeting Italy using phishing emails designed to deploy information-stealing programs on compromised Windows systems.
Uptycs security researcher Karthickkumar Kathiresan said in the report:
Campaign details first disclosed Milan-based IT services company SI.net made the announcement last month.
The multi-stage infection sequence begins with an invoice-themed phishing email. Click the link to download a password-protected ZIP archive file. This file contains his two files, a shortcut (.LNK) file and a batch (.BAT) file. File.
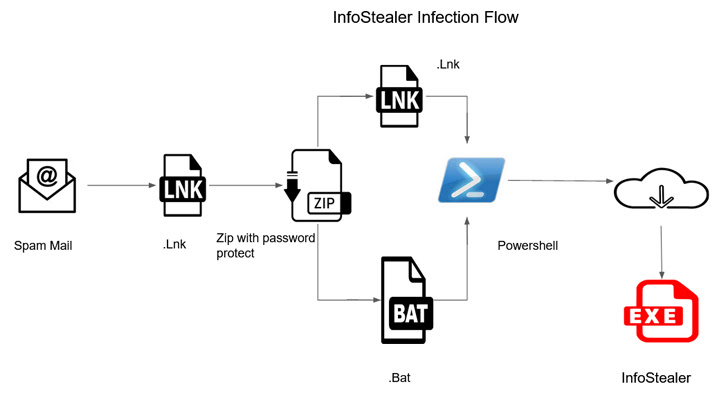
The attack chain remains the same regardless of which file is launched. This is because opening the shortcut file fetches the same batch script designed to install the information stealer payload from the GitHub repository. This is achieved by utilizing legitimate PowerShell binaries that are also obtained from GitHub.
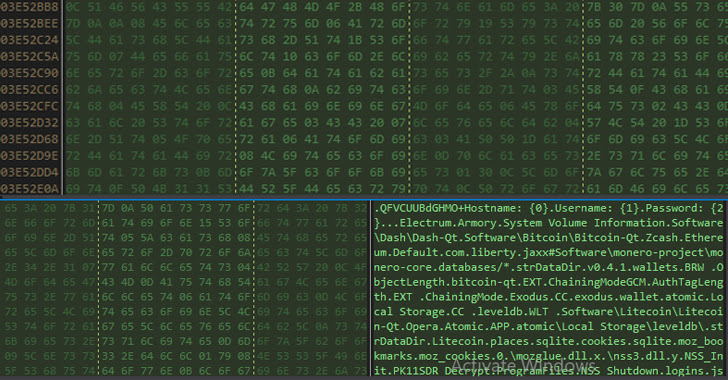
Once installed, the C#-based malware collects system metadata, information from numerous web browsers (cookies, bookmarks, credit cards, downloads, credentials, etc.), and multiple cryptocurrency wallets, all of which sent to the attacker. domain managed by
To mitigate such attacks, organizations are encouraged to implement “rigorous security controls and multi-layered visibility and security solutions to identify and detect malware.”









