A serious security flaw was discovered in the open source jsonwebtoken (JWT) library. Successful exploitation could lead to remote code execution on the target server.
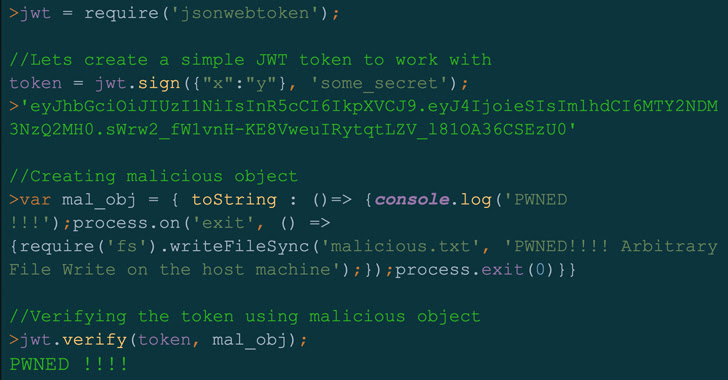
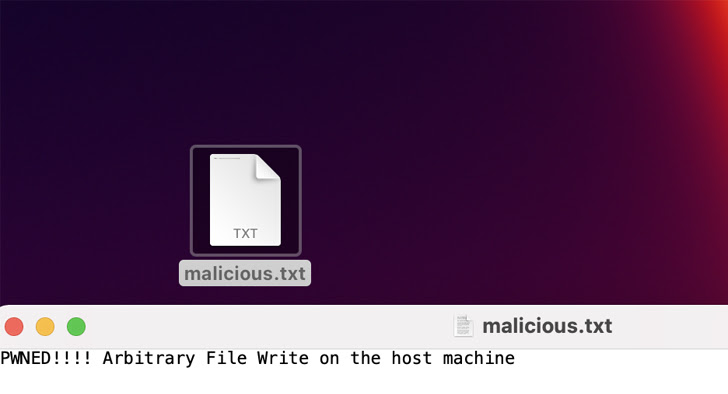
In a report on Monday, Artur Oleyarsh, a researcher at Palo Alto Networks Unit 42, said, “By exploiting this vulnerability, an attacker could perform remote code execution (RCE) on the server, creating a malicious may validate a JSON Web Token (JWT) request that has been encrypted.
tracked as CVE-2022-23529 (CVSS score: 7.6), this issue affects all versions of the library, including 8.5.1, and is addressed in version 9.0.0, which shipped on December 21, 2022. The flaw was reported to him by a cybersecurity firm on July 13th. , 2022.
Developed and maintained by Okta’s Auth0, jsonwebtoken is a JavaScript that allows users to decode, validate, and generate JSON Web Tokens as a means of securely transmitting information between two parties for authorization and authentication. Module. Over 10 million downloads every week on the npm software registry and used in over 22,000 projects.
Therefore, the ability to execute malicious code on a server violates confidentiality and integrity guarantees, allowing a malicious person to overwrite arbitrary files on the host and use a compromised private key to arbitrarily You may be able to take action.
“Having said that, to exploit the vulnerability described in this post to control the value of secretOrPublicKey, an attacker would have to exploit a flaw in the secret management process,” Oleyarsh explained. doing.
As open source software increasingly emerges as a lucrative initial access vector for threat actors to mount supply chain attacks, vulnerabilities in such tools need to be proactively identified, mitigated, and patched by downstream users. It is important to apply
To make matters worse, cybercriminals have become much faster at exploiting newly revealed flaws, and the time between patch release and exploitation has been significantly reduced. According to Microsoft, it only takes an average of 14 days from the time a bug is made public until the exploit is actually detected.
To address this vulnerability discovery problem, Google last month launched OSV -Announced the release of Scanner.











