
A wave of Gootkit malware loader attacks is targeting the Australian healthcare sector with the help of legitimate tools such as VLC Media Player.
Gootkit, also known as Gootloader, is known to employ search engine optimization (SEO) poisoning tactics (aka spamdex) for initial access. It usually works by compromising and exploiting legitimate infrastructure and seeding those sites with common keywords.
Like other malware of its kind, Gootkit can steal data from browsers and perform adversary-in-the-browser (AitB) attacks, keylogging, taking screenshots, and other malicious actions.
New research from Trend Micro reveals that the keywords “hospital,” “health,” “medical care,” and “corporate contract” are combined with various city names in Australia, suggesting that the malware is targeting accounting firms and It shows that we are expanding beyond the law firm.
The attack starts by luring users searching for the same keyword to an infected WordPress blog to download a malware-laced ZIP file.
“When visiting the site, users are presented with a screen disguised as a legitimate forum,” said Trend Micro researchers. “Users are enticed to visit a link so that they can download a malicious ZIP file.”
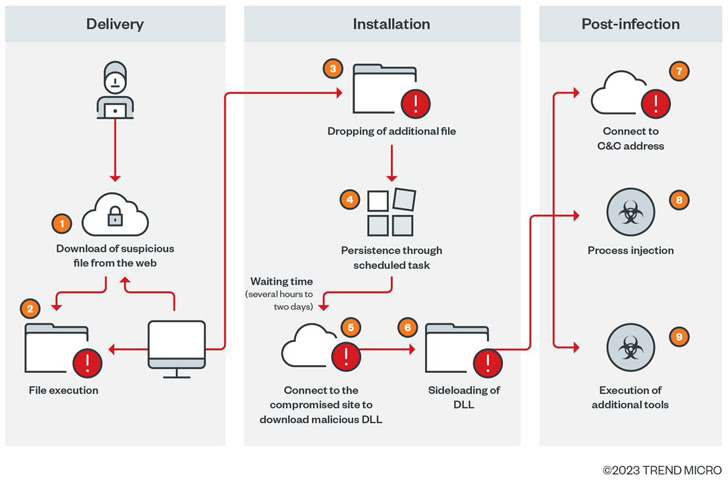
Additionally, the JavaScript code used to carry out this ruse is injected into valid JavaScript files in random sections of the compromised website.
The downloaded ZIP archive not only uses obfuscation at runtime to avoid analysis, but also contains JavaScript files used by scheduled tasks to establish persistence on the machine.
The execution chain then leads to a PowerShell script designed to retrieve files from remote servers and perform post-exploitation activities. The script only starts after a few hours to his two day waiting period.
“This latency, which clearly distinguishes the initial and second stages of infection, is a distinguishing feature of Gootkit loader behavior,” said the researchers.
After the wait time, two additional payloads are dropped: msdtc.exe and libvlc.dll. The former is a legitimate VLC Media Player binary used to load the Cobalt Strike DLL component, which then downloads more tools to facilitate detection.
“Malicious actors behind [Gootkit] “Threats targeting specific occupations, industries and geographies are becoming more aggressive,” researchers said.









