
A new analysis of Raspberry Robin’s attack infrastructure reveals that other attackers may be able to repurpose the infection for malicious activity, making the threat even more potent.
Raspberry Robin (also known as the QNAP worm), by a threat actor dubbed DEV-0856, is malware that is gaining increasing attention due to its use in attacks targeting financial, government, insurance, and telecommunications entities.
Pay-per-install (PPI) bots that can deliver next-stage payloads, given that multiple actors are used to drop different payloads such as SocGholish, Bumblebee, TrueBot, IcedID, and LockBit ransomware I suspect it’s the net.
Raspberry Robin, in particular, uses infected USB drives as a propagation mechanism and leverages compromised QNAP Network Attached Storage (NAS) devices as a first-level command and control (C2).
Cybersecurity firm SEKOIA said it was able to identify at least eight virtual private servers (VPS) hosted on Linode. These act as his second C2 layer that may act as a forward proxy to the as-yet-unknown next layer.
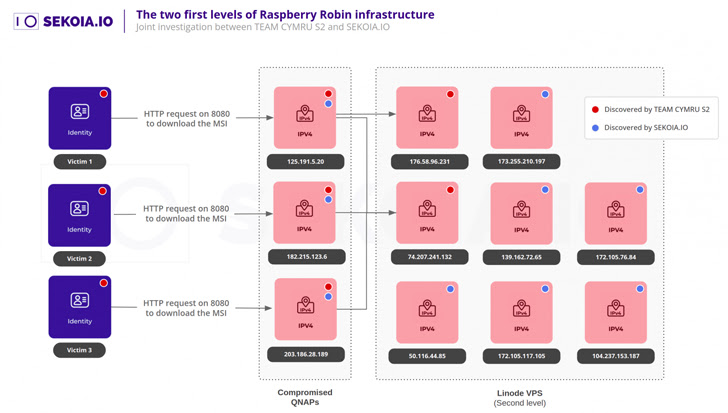
“The compromised QNAP appears to act as a validator and forwarder, respectively,” said the French-based company. “If the received request is valid, it will be redirected to the upper infrastructure.”
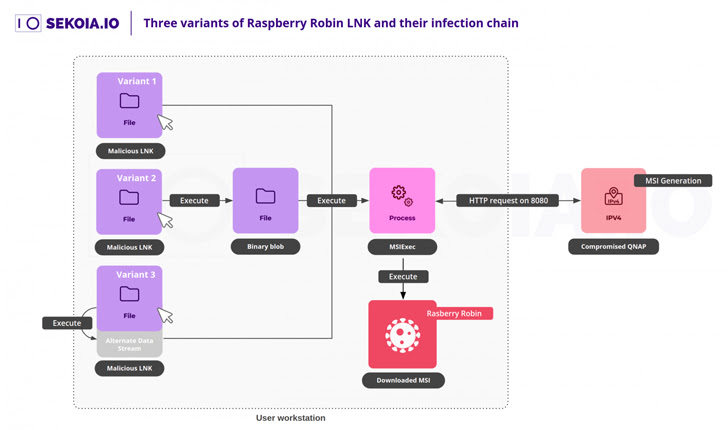
The attack chain thus unfolds as follows: When a user inserts a USB drive and launches a Windows shortcut (.LNK) file, the msiexec utility is launched to download her main obfuscated Raspberry Robin payload from her QNAP instance.
Reliance on msiexec to send HTTP requests to retrieve malware can be used to hijack such requests and send them to another rogue, either through a DNS hijacking attack or by purchasing a previously known domain after expiration. MSI payload can be downloaded.
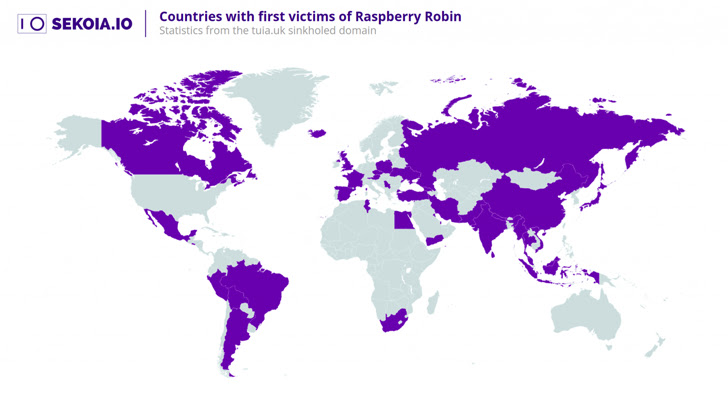
One such domain is tiua.[.]uk was registered early in the campaign in late July 2021 and was used as C2 from 22 September 2021 to 30 November 2022 and suspended by the .UK Registry.
“By pointing this domain into a sinkhole, we were able to obtain telemetry from one of the domains originally used by the Raspberry Robin operator” for malicious activity. “
The exact cause of how the first wave of Raspberry Robin USB infections arose is currently unknown, but it is possible that it was achieved by relying on other malware to spread the worm. It is believed that there is.
This hypothesis is proven by the presence of a .NET spreader module that is said to be responsible for distributing Raspberry Robin .LNK files from infected hosts to USB drives. These .LNK files then compromise other machines in the manner previously described.
The development is that Google’s Mandiant repurposed an expired domain associated with the ANDROMEDA malware by the Russian-affiliated Turla group to deliver reconnaissance and backdoor tools to targets compromised by the latter in Ukraine. A few days after the reveal of
“Botnets have multiple purposes, can be reused and/or modified by operators, and can even be hijacked by other groups over time,” the researchers said.









