
Security researchers have uncovered multiple architectural vulnerabilities in Siemens SIMATIC and SIPLUS S7-1500 programmable logic controllers (PLCs). This vulnerability could be exploited by malicious attackers to covertly install firmware on affected devices and take control over them.
discoverer red balloon securitythe issue is tracked as CVE-2022-38773 (CVSS score: 4.6), the low severity is due to the assumption that exploitation requires physical tampering with the device.
The flaw “could allow an attacker to bypass all protected boot functions, resulting in arbitrary and permanent modification of operating code and data,” the company said. Over 100 models are affected.
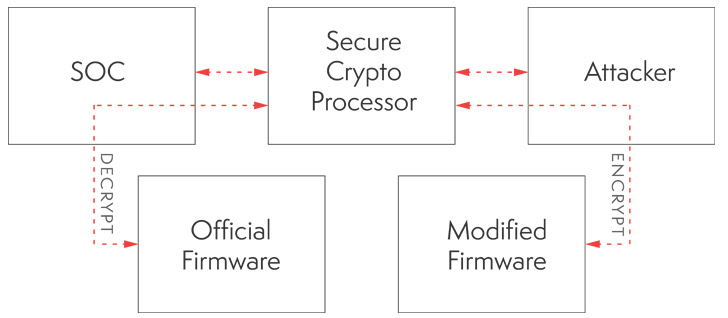
Put another way, the vulnerability is the result of a lack of asymmetric signature verification of the firmware at boot time, effectively allowing an attacker to load a compromised bootloader and firmware, thus reducing integrity protection. weaken it.
The more serious consequences of loading such modified firmware could allow an attacker to permanently execute malicious code and gain complete control of the device without signaling red flags. There is something.
“This discovery has significant implications for industrial environments, as an unpatched hardware root-of-trust vulnerability could permanently and arbitrarily modify the operating code and data of the S7-1500. may give,” said the researchers.
In an advisory issued this week, Siemens said it was not planning a patch, but advised customers to limit physical access to affected PLCs to trusted personnel to avoid hardware tampering. urged to
The lack of firmware updates is because the cryptography behind the Protected Boot feature is built into a dedicated physical secure element chip (called an ATECC108 CryptoAuthentication coprocessor) that decrypts the firmware in memory at boot time. .
Therefore, an attacker with physical access to the device could exploit the identified issues in the encryption implementation to decrypt the firmware, tamper with it, and exploit any known remote code execution flaws, either physically or by exploiting known remote code execution flaws. can be exploited to flash Trojanized firmware into the PLC.
“Underlying Vulnerability — Improper Hardware Implementation of [Root of Trust] It uses a dedicated cryptographic processor and the hardware cannot be physically changed, so it cannot be patched and cannot be fixed by firmware updates,” the researchers explained.
However, the German automation giant said it was in the process of releasing a new hardware version of its S7-1500 product family with an improved “secure boot mechanism” that addresses the vulnerability.
The findings last year affected Siemens SIMATIC devices, which could be exploited by industrial security company Claroty to obtain a hardcoded global secret encryption key to completely compromise the product. It is due to revealing a serious defect that gives









