Zoho ManageEngine users are asked to patch their instances for critical security vulnerabilities prior to the proof of concept release (PoC) exploit code.
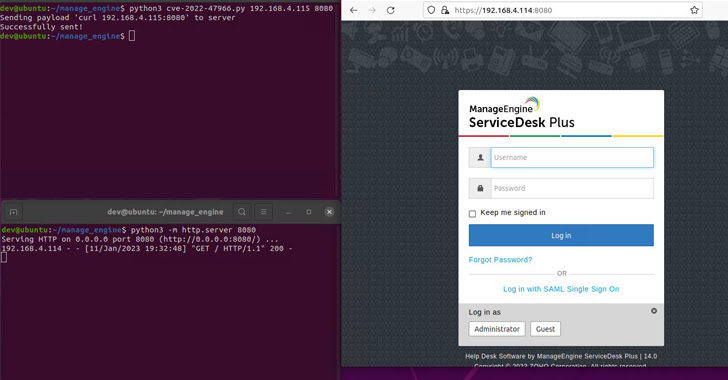
The problem is that CVE-2022-47966is an unauthenticated remote code execution vulnerability that affects multiple products through the use of an older third-party dependency, Apache Santuario.
“This vulnerability allows an unauthenticated adversary to execute arbitrary code,” Zoho warned in an advisory issued late last year that enabled SAML single sign-on (SSO) functionality. becoming or past.
Horizon3.ai has now released an Indication of Compromise (IOC) related to this flaw, stating that they were able to successfully reproduce the exploit against their ManageEngine ServiceDesk Plus and ManageEngine Endpoint Central products.
“This vulnerability is easy to exploit and is a good candidate for attackers to ‘spray and play’ on the Internet,” said researcher James Horseman. “This vulnerability could allow remote code execution as NT AUTHORITY\SYSTEM, essentially giving an attacker complete control of the system.”
Possessing such elevated privileges, an attacker could weaponize it to steal credentials for the purpose of performing lateral movement, the San Francisco-based company said, adding that attackers could use special Added that the exploit would need to be triggered by sending a crafted SAML request to
Horizon3.ai further draws attention to the fact that there are currently over 1,000 SAML-enabled ManageEngine product instances exposed to the Internet, making them potentially lucrative targets. bottom.
It is not uncommon for hackers to exploit awareness of key vulnerabilities in malicious campaigns. Therefore, it is essential to install the fix as soon as possible regardless of your SAML configuration.











