Security vulnerabilities have been revealed in Netcomm and TP-Link routers. Some of these routers can be weaponized to execute code remotely.
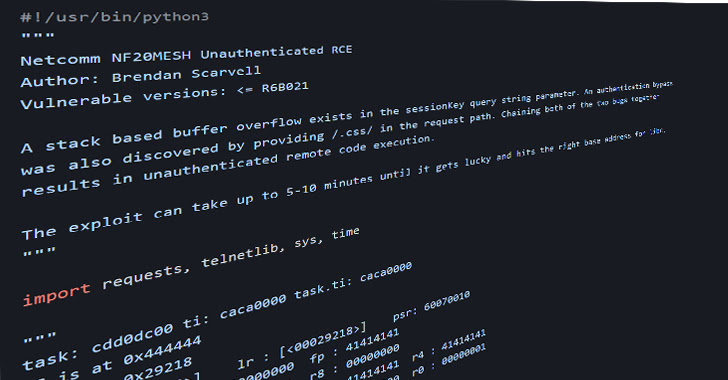
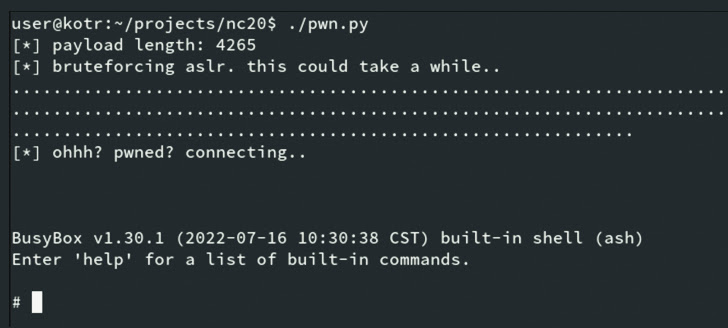
The flaws tracked as CVE-2022-4873 and CVE-2022-4874 involve stack-based buffer overflow and authentication bypass cases on Netcomm router model NF20MESH running software versions prior to R6B035. , NF20, and NL1902.
The CERT Coordination Center (CERT/CC) said in an advisory released on Tuesday that “these two vulnerabilities can be chained together to allow an unauthenticated, remote attacker to execute arbitrary code.” increase.
“Attackers can first gain unauthorized access to affected devices and then use those entry points to gain access to other networks or to compromise the availability, integrity, or integrity of data transmitted from the internal network. , or violate confidentiality.”
Security researcher Brendan Scarvell is credited for discovering and reporting the issue in October 2022.
In a related development, CERT/CC discovered an information disclosure (CVE-2022-4499) and remote code execution (CVE-2022- 4498).
CVE-2022-4499 is also a side-channel attack targeting functionality used to validate entered credentials. The CERT/CC said, “Measuring the response time of vulnerable processes may make it easier to guess each byte of a username and password string.
Microsoft researcher James Hull is credited with disclosing two bugs. The Hacker News has reached out to his TP-Link for comment and will update the article when we hear back.











