dubbing campaign in progress earth bogle uses geopolitical-themed lures to deliver the NjRAT remote access Trojan to victims in the Middle East and North Africa.
“Attackers are using public cloud storage services such as files.[.]fm and file[.]lv hosts malware, while compromised web servers distribute NjRAT,” Trend Micro said in a report published Wednesday.
Phishing emails crafted to the victim’s interests typically contain malicious attachments that launch infection routines. It takes the form of a Microsoft Cabinet (CAB) archive file containing a Visual Basic Script dropper to deploy the next stage payload.
Alternatively, the files are suspected to be distributed through social media platforms such as Facebook or Discord, and in some cases even creating fake accounts to display ads on pages impersonating legitimate news outlets. I have.
A CAB file hosted on a cloud storage service masquerades as a sensitive voice call that tricks the victim into opening the archive, and another VBScript file that disguises itself as an image file just to execute the VBScript. Get
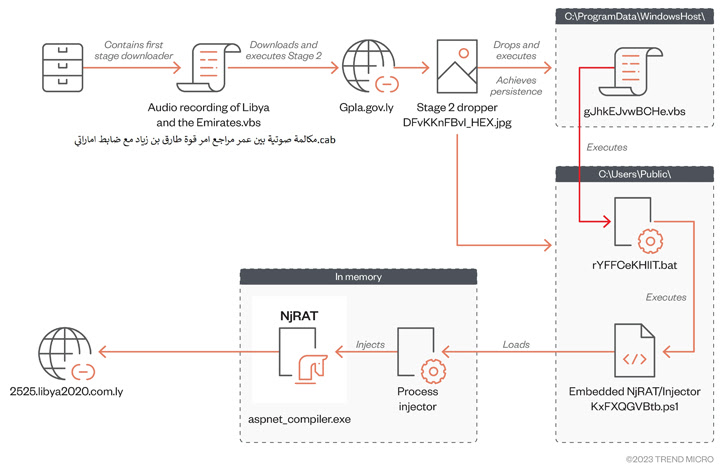
The second stage VBScript fetches a PowerShell script from the already compromised domain that loads the RAT payload into memory and executes it.
First discovered in 2013, NjRAT, also known as Bladabindi, has a myriad of features that allow attackers to gather sensitive information and gain control over compromised computers.
“This case demonstrates how attackers are leveraging public cloud storage as malware file servers, combined with social engineering techniques that appeal to people’s emotions, such as local geopolitical themes, to infect target populations.” concludes the researchers.











