
Vulnerability analysis results from Orange Cyberdefenses’ Security Navigator show that several vulnerabilities, first discovered in 1999, are still being found in networks today. This is a concern.
Age of VOC findings
Our vulnerability scans are performed regularly. This allows you to see the difference between when a scan is run against an asset and when a particular finding is reported on that asset. You can call it “age”. If the first reported finding is not addressed, it will occur in more scans over time, so we can track how the age of the reported findings changes over time .
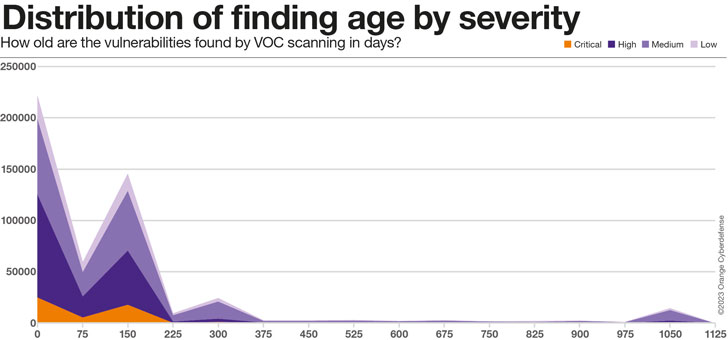
As the chart below clearly shows, at all severity levels, the majority of the actual findings in the dataset are between 75 and 225 days old. There is a second “peak” at about 300 days, which can be ignored as it is believed to be related to the age of the data in the dataset. Finally, at about 1,000 days you will see an attractive ‘bump’. We believe this represents the ‘long tail’ of our findings in the dataset.
75% of 1000-day “bump” findings are of moderate severity, while 16% are classified as high or critical severity.
The average age of the dataset results is subject to changes in the customer and asset set as well as external factors, as seen in the high degree of variability. Yet, in the 24 months since onboarding a client to the platform, there has been a clear 241% increase in the average age of the survey findings, from his 63 days to 215 days.
Loosely grouping the findings identified from the vulnerability scan data by ‘age group’ reveals the following:
- Only 20% of all findings can be addressed within 30 days
- 80% of all findings take 30+ days to patch
- 57% of all findings take more than 90 days to patch.
- 215-day average
Average/maximum age of findings by severity
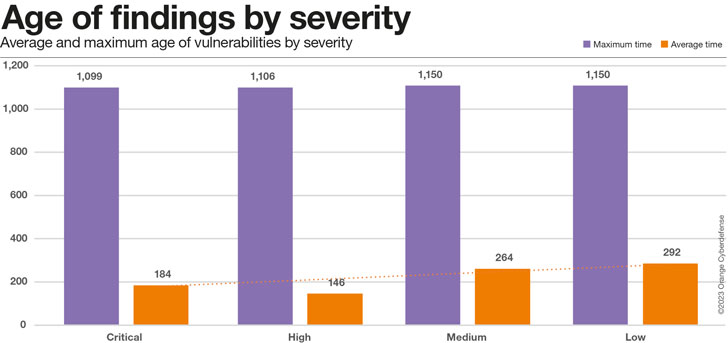
The chart below suggests that even critical vulnerabilities take an average of about six months to resolve, which is at least 36% faster than the time for less severe issues.
A closer look at the average and maximum time measurements for different severity ratings yields the graph below.
Our conclusion that critical problems are resolved more quickly is based on mean relaxation times, but maximum times are consistently longer, regardless of severity.
This metric should be monitored further as the dataset grows in the future.
Industry comparison
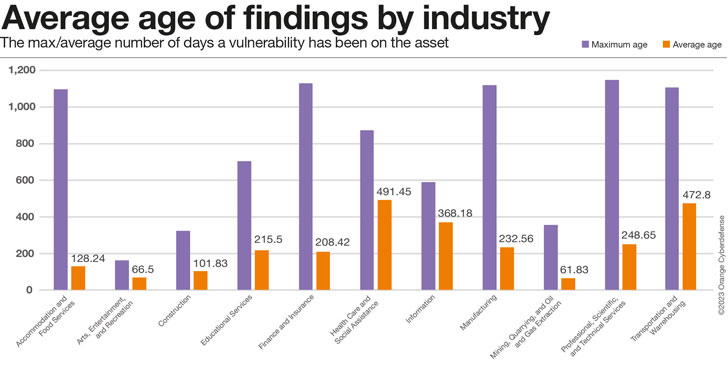
The maximum age of the findings in the view below is just as useful as an indication of how long customers in that industry have been in the data set, but the average age tells us how well the customer copes with the problem. Is there a better proxy to show you? report. Thus, industries with high maximums and low averages have the best results, while industries with high maximums and high averages… are the “worst” industries. Industries with very low maximum age probably have not been in the dataset for a long time and should not be included in the comparison for this indicator.
However, age found is an important indicator when comparing these industries.
How old are those vulnerabilities really?
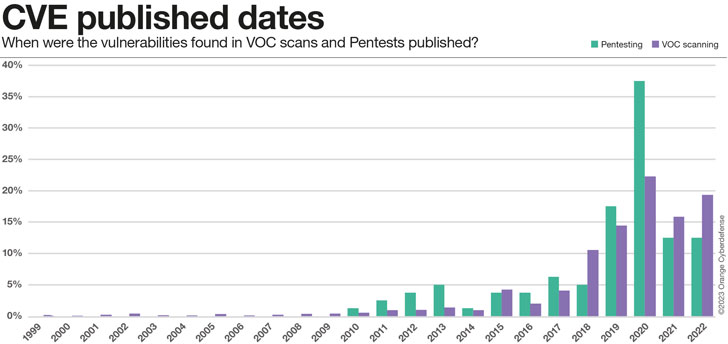
So far, we’ve only looked at the relative time from when we first discovered the asset vulnerability to now (if any). However, it doesn’t give us any information on how old these vulnerabilities really are. You can take a closer look at the CVEs found and analyze their release dates. The results are somewhat puzzling, but seem to be consistent with the unfolding situation. For some reason some vulnerabilities have not been fixed. They become part of the guaranteed liability that companies accumulate.
- 0.5% of reported CVEs are over 20 years old
- 13% of CVE reports are over 10 years old
- 47% of CVEs are older than 5 years
Conclusion
Over 22 vulnerabilities with assigned CVEs are published daily. With an average CVSS score of over 7 (High Severity), each of these disclosed vulnerabilities is an important data point that influences the risk equation and actual threat exposure.
Vulnerability scanning and penetration testing are the mechanisms we use to understand vulnerabilities that can affect our security posture, understand their potential impact, prioritize them and take appropriate action . Although these two assessment exercises have different approaches, they use similar language and serve similar purposes.
This year, we are including analysis of datasets from both services in the navigator. This is the first attempt and the data is still far from complete.
What we do know is that we struggle with managing known vulnerabilities. It takes an average of 215 days to patch reported vulnerabilities. This is slightly lower for critical vulnerabilities. These seem to patch 36% faster than Low severity issues. But the big picture remains grim. 80% of the overall findings took 30 days or more to apply the patch, and 57% took him 90 days or more.
Our penetration testing team is still finding vulnerabilities that were first identified in 2010, and our scanning team has encountered issues dating back to 1999. In fact, 47% of CVEs are older than 5 years. 13% are over the age of 10. This is a worrisome result.
This is an analysis excerpt. Details such as vulnerability severity and changes in pentest and VOC scan results over time (among many other interesting research topics) can be found in Security Navigator. It’s free, so please take a look. worth it!
Note: This informative article is expertly crafted and generously shared by Charl van der Walt, Head of Security Research at Orange Cyberdefense.











