Since at least August 2022, cybersecurity researchers have discovered a new Python-based attack campaign that utilizes a Python-based Remote Access Trojan (RAT) to take control of compromised systems.
In a report shared with The Hacker News, Securonix said, “This malware is unique in that it evades detection and utilizes WebSockets for both command and control (C2) communication and information exfiltration.”
Named PY#RATION by the cybersecurity firm, the malware comes with a number of features that allow attackers to gather sensitive information. Recent versions of the backdoor also have anti-evasion techniques, suggesting they are being actively developed and maintained.
The attack begins with a phishing email containing a ZIP archive. The email contains two shortcut (.LNK) files masquerading as images of the front and back of a seemingly legitimate UK driver’s license.
Opening each .LNK file retrieves two text files from the remote server. These files are later renamed to .BAT files and run covertly in the background while the decoy image is displayed to the victim.
The C2 server also downloads another batch script designed to retrieve additional payloads from the server, including a Python binary (“CortanaAssistance.exe”). The choice to use Cortana, Microsoft’s virtual assistant, represents an attempt to disguise malware as a system file.
Two versions of this Trojan were detected: versions 1.0 and 1.6. The new variant adds about 1,000 lines of code, supports network scanning capabilities to reconnoit compromised networks, and hides Python code behind an encryption layer. Fernet module.
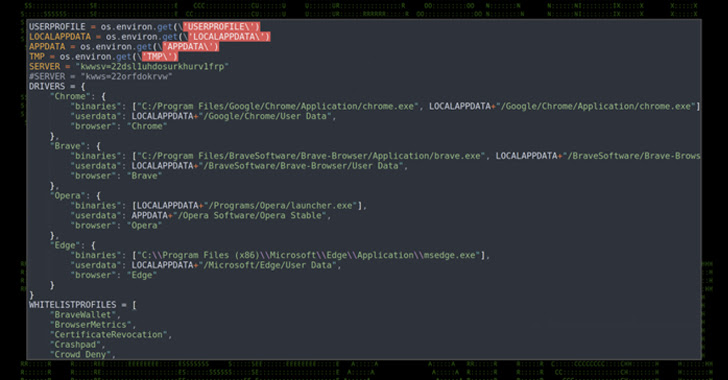
Other notable features include file transfer from host to C2 or vice versa, recording keystrokes, executing system commands, extracting passwords and cookies from web browsers, capturing clipboard data, presence of antivirus software check etc.
Additionally, PY#RATION serves as a conduit for deploying more malware, consisting of another Python-based infostealer designed to siphon data from web browsers and cryptocurrency wallets. .
The attacker’s origin remains unknown, but the nature of the phishing lure suggests that the intended target is likely in the United Kingdom or North America.
“The PY#RATION malware is not only relatively difficult to detect, but it is also very flexible as it is a Python-compiled binary that can be run on almost any target, including Windows, OSX and Linux variants.” said researchers Den Iuzvyk and Tim. Peck, and Oleg Kolesnikov said.
“The fact that the attackers utilized layers of fernet encryption to hide their original source compounds the difficulty of detecting known malicious strings.”











