
North Korean government-backed threat actors are linked to attacks targeting South Korean and US government and military officials, think tanks, policy makers, academics and researchers
Google’s Threat Analysis Group (TAG) tracks clusters under the following names: islandThis is said to be a subset of another threat group Mandiant tracks under the name APT43.
The company said it began monitoring hacking crews in 2012, adding that it “observed target individuals from groups with expertise in North Korean policy issues such as sanctions, human rights and non-proliferation issues.”
APT43, and therefore ARCHIPELAGO,’s priorities are said to be aligned with a major foreign intelligence agency, North Korea’s Reconnaissance General Bureau (RGB), and have been shown to overlap with the group popularly known as Kimsuky. suggesting.
The attack chain mounted by ARCHIPELAGO involves the use of phishing emails containing malicious links that, when clicked by recipients, redirect them to fake login pages designed to harvest credentials.
These messages purport to be from news outlets and think tanks, and attempt to entice targets on the pretext of requesting interviews or additional information about North Korea.
“ARCHIPELAGO spends time and effort building trust with its targets, often exchanging emails for days or weeks before finally sending malicious links or files,” says TAG. said.
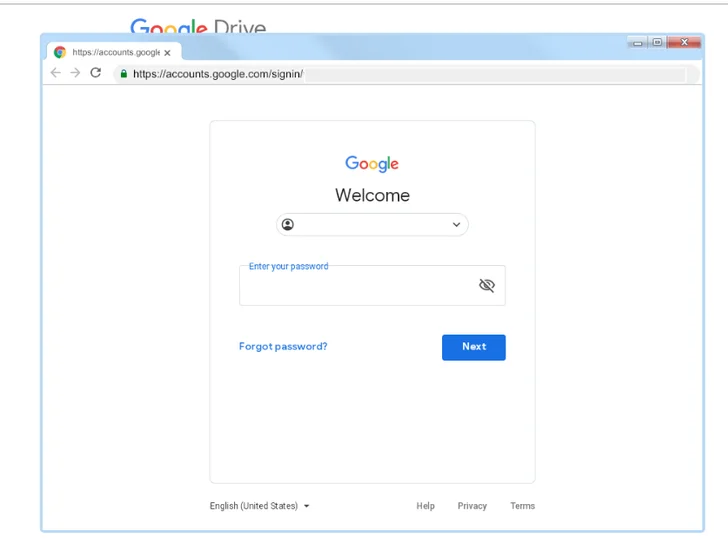
This threat actor is also known to use browser-in-the-browser (BitB) techniques to display a malicious login page inside a real window and steal credentials.
Additionally, phishing messages masquerade as Google account security alerts to activate infections, with hostile groups hosting BabyShark-like malware payloads in the form of blank files or ISO optical disc images on Google Drive. increase.
Learn How to Secure Your Identity Perimeter – A Proven Strategy
Improve your business security in our upcoming expert-led cybersecurity webinar: Exploring Identity Perimeter Strategies!
Don’t miss it – secure your seat!
Another notable technique employed by ARCHIPELAGO is the use of rogue Google Chrome extensions to collect sensitive data. This has been proven in previous campaigns called Stolen Pencil and SharpTongue.
The development began when the AhnLab Security Emergency Response Center (ASEC) detailed how Kimsuky used Alternate Data Streams (ADS) and weaponized Microsoft Word files to deliver information-stealing malware. I was.











