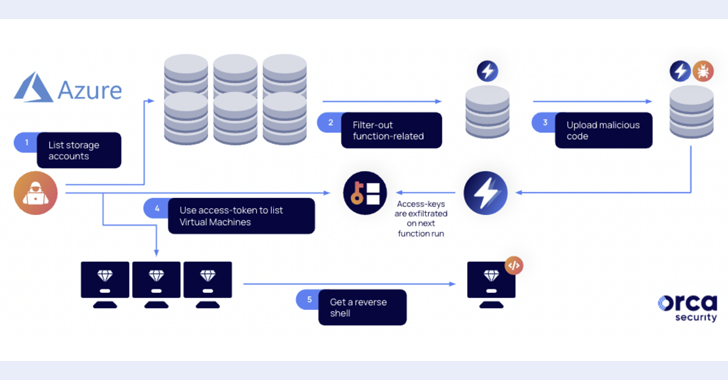
“Design flaws” discovered in Microsoft Azure can be exploited by attackers to gain access to storage accounts, lateral movement within the environment, and even remote code execution.
“Manipulating Azure Functions to steal higher-privileged access tokens, move laterally, access critical business assets, or execute remote code (RCE) can compromise Microsoft storage. Accounts can be abused and leveraged,” Orca said in a new report shared. at Hacker News.
The exploitation path underlying this attack is a mechanism called shared key authentication that is enabled by default on storage accounts.
According to Microsoft, Azure generates two 512-bit storage account access keys when creating a storage account. These keys can be used to authorize access to data through shared key authentication or SAS tokens signed with a shared key.
“The storage account access key provides full access to the configuration and data of the storage account,” Microsoft says in its documentation. “Accessing the shared key gives the user full access to the configuration of the storage account and its data.”
According to the cloud security firm, these access tokens can be stolen by manipulating Azure Functions, allowing an attacker with access to accounts with the Storage Account Contributor role to escalate privileges and take over the system. It is said that there is
Specifically, calling a function app with a managed identity can be exploited to execute arbitrary commands. This is made possible by the fact that a dedicated storage account is created when you deploy your Azure Function App.
“If an attacker finds a function app’s storage account with a strong managed identity assigned to it, they can execute code on their behalf, resulting in a subscription privilege escalation (PE),” said Roi, a researcher at Orca. Nisimi said.
Learn How to Secure Your Identity Perimeter – A Proven Strategy
Improve your business security in our upcoming expert-led cybersecurity webinar: Exploring Identity Perimeter Strategies!
Don’t miss it – secure your seat!
This means that by exfiltrating the access token of the managed identity assigned to the Azure Function app to a remote server, the attacker can elevate privileges, move laterally, access new resources, and reverse-shell on the virtual machine. can do.
“By overriding a function file in a storage account, an attacker can steal and steal a higher privileged identity and use it to move laterally and exploit the victim’s most precious crown jewel. can be infringed,” explains Nisimi.
As a mitigation, we recommend that organizations consider disabling Azure Shared Key authentication and using Azure Active Directory authentication instead. In a coordinated disclosure, Microsoft said it has “plans to update how Functions client tools work with storage accounts.”
“This includes changes to better support scenarios using identities. After identity-based connectivity for AzureWebJobsStorage is generally available and new experiences are validated, identities will become the default mode for AzureWebJobsStorage This is intended to move away from shared key authentication.” Added more tech giants.
The findings highlight a misconfiguration issue affecting Azure Active Directory that allows Bing search results to be tampered with, and an Azure Service Fabric Explorer (SFX) vulnerability that can lead to unauthenticated remote code execution. It arrived a few weeks after Microsoft patched the reflected XSS vulnerability.