Attackers using hacking tools from an Israeli surveillance ware vendor named QuaDream targeted at least five members of civil society in North America, Central Asia, Southeast Asia, Europe and the Middle East.
A group of Citizen Lab researchers found that spyware campaigns targeted journalists, opposition figures, and NGO workers in 2021. The victim’s name has not been released.
There are also suspicions that the company used an exploit called a zero-click attack. end of the world iOS 14 deploys spyware as a zero-day with versions 14.4 and 14.4.2. After March 2021, there is no evidence that the exploit has been used.
ENDOFDAYS “appears to utilize an invisible iCloud calendar invitation sent to the victim by the spyware operator,” the researchers said.
The Microsoft Threat Intelligence team tracks QuaDream as follows: DEV-0196, describes cyber mercenary firms as Private Sector Offensive Actors (PSOA). QuaDream is not directly involved in targeting, but is known to sell “exploit services and malware” to government customers.
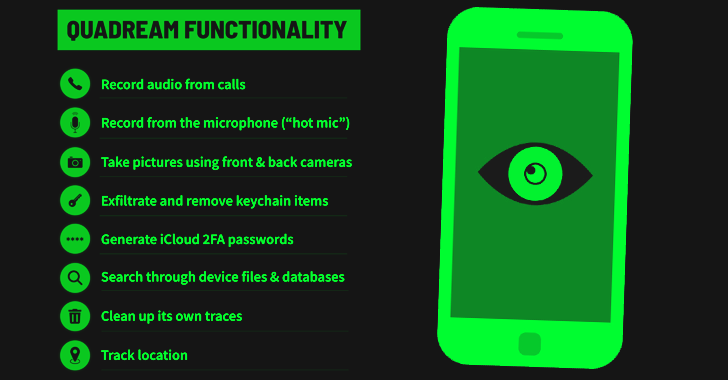
malware named Kingspawncontains a monitoring agent and a primary malware agent, both Mach-O files written in Objective-C and Go respectively.
Monitoring agents are responsible for reducing the forensic footprint of malware to evade detection, while main agents include device information, cellular and Wi-Fi data collection, file collection, background camera Access to, location access, and call log functions. Generate time-based one-time passwords (TOTPs) for , iOS Keychain, and even iCloud.

Other samples support recording audio from phone calls and microphones, running queries on SQL databases, and cleaning up forensic trails (such as deleting all calendar events two years ago from the current time). increase. Data is exfiltrated via HTTPS POST requests.
Internet scans conducted by Citizen Lab show that QuaDream customers will be coming from several countries around the world in late 2021 and early 2023, including Bulgaria, Czech Republic, Hungary, Romania, Ghana, Israel, Mexico, Singapore, and the UAE. It was revealed that they were operating 600 servers. Uzbekistan.
Despite the spyware’s attempts to cover up its tracks, the interdisciplinary lab has found unspecified tracks of what it calls an “ectoplasmic agent” that could be used to track QuaDream’s toolset in the future. He said he was able to discover
This isn’t the first time QuaDream has made headlines. In February 2022, Reuters reported that the company had weaponized his FORCEDENTRY zero-click exploit in iMessage and deployed a spyware solution named REIGN.
Then, in December 2022, Meta revealed that it had taken down a network of 250 Facebook and Instagram fake accounts controlled by QuaDream, infecting Android and iOS devices and stealing personal data.
Learn How to Secure Your Identity Perimeter – A Proven Strategy
Improve your business security in our upcoming expert-led cybersecurity webinar: Exploring Identity Perimeter Strategies!
Don’t miss it – secure your seat!
If anything, the development shows that despite the notoriety that has been attracted to the NSO group, commercial spyware companies continue to keep a low profile and develop sophisticated spyware products for use by government clients. I’m here.
“Until the uncontrolled proliferation of commercial spyware is successfully curbed by systematic government regulation, the number of cases of abuse is likely to continue to grow, with companies with big names and those still operating in the shadows. It will be fueled both by other companies that have
Microsoft has called the growth of mercenary spyware companies a threat to democracy and human rights, saying it will require “collective efforts” and “cooperation of multiple stakeholders” to combat such attackers. .
“Additionally, it is only a matter of time before the tools and technologies they sell become more widely used,” said Amy Hogan-Burney, the company’s deputy general counsel for cybersecurity policy and protection.
“This poses serious risks not only to human rights online, but also to the security and stability of the broader online environment. We need to find new ways to access it.”