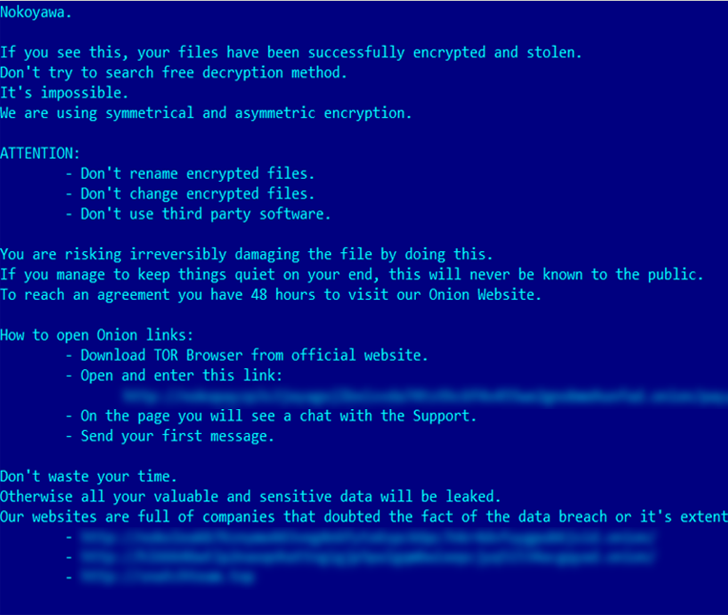
On the second Tuesday of this month, Microsoft released another series of security updates to fix a total of 97 flaws affecting its software. One of them is being actively exploited in real-world ransomware attacks.
Of the 97 bugs, 7 are rated Critical and 90 are rated Important. Interestingly, 45 of the flaws are remote code execution flaws, followed by privilege escalation vulnerabilities at 20. This update also follows fixes for 26 vulnerabilities in the Edge browser released over the past month.
An actively exploited security flaw is CVE-2023-28252 (CVSS score: 7.8), a privilege escalation bug in the Windows Common Log File System (CLFS) driver.
In an advisory, Microsoft said, “An attacker who successfully exploited this vulnerability could gain SYSTEM privileges,” and credits researchers Boris Larin, Genwei Jiang, and Quan Jin for reporting the issue. I admit it.
CVE-2023-28252 is CVE-2022-24521, CVE-2022-37969, and CVE-2023-23376 (CVSS score: 7.8 ). At least 32 vulnerabilities have been identified in CLFS since 2018.
According to Russian cybersecurity firm Kaspersky, the vulnerability has been weaponized by cybercriminal groups deploying the Nokoyawa ransomware against small businesses in the Middle East, North America, and Asia.
“CVE-2023-28252 is an out-of-bounds write (increment) vulnerability that can be exploited when the system attempts to extend metadata blocks,” Larin said. “This vulnerability is triggered by manipulation of the base log file.”
In light of the ongoing exploitation of the vulnerability, CISA has added Windows zero-days to its catalog of known exploited vulnerabilities (KEV), and by May 2, 2023, to Federal Civil Administration (FCEB) agencies. I ordered the system to be secured.
Also patches critical remote code execution flaws affecting the DHCP Server service, Layer 2 Tunneling Protocol, Raw Image Extension, Windows Point-to-Point Tunneling Protocol, Windows Pragmatic General Multicast, and Microsoft Message Queuing (MSMQ). applies.
The MSMQ bug, tracked as CVE-2023-21554 (CVSS score: 9.8) and named QueueJumper by Check Point, allows malicious code to be executed by sending specially crafted malicious MSMQ packets to the MSMQ server. It can cause execution and take over the server.
“The CVE-2023-21554 vulnerability could allow an attacker to reach on TCP port 1801 and execute code remotely without authentication,” said Check Point researcher Haifei Li. “In other words, an attacker could use an exploit to gain control of a process via her single packet to her 1801/tcp port, triggering the vulnerability.”
Two other flaws found in MSMQ, CVE-2023-21769 and CVE-2023-28302 (CVSS score: 7.5), can be exploited to cause denial of service (DoS) conditions such as service crashes and Windows blue screens. may occur. Death (BSoD).
Learn How to Secure Your Identity Perimeter – A Proven Strategy
Improve your business security in our upcoming expert-led cybersecurity webinar: Exploring Identity Perimeter Strategies!
Don’t miss it – secure your seat!
Microsoft has also updated its advisory for CVE-2013-3900, the WinVerifyTrust Signature Verification Vulnerability, to include the following Server Core installation versions –
- Windows Server 2008 Service Pack 2 for 32-bit systems
- Windows Server 2008 Service Pack 2 for x65-based Systems
- Windows Server 2008 R2 Service 1 for x64-based Systems
- Windows Server 2012
- Windows Server 2012 R2
- Windows Server 2016
- Windows Server 2019, and
- Windows Server 2022
This development is based on observations that North Korea-related attackers have used this flaw to embed encrypted shellcode into legitimate libraries without disabling Microsoft-issued signatures. was broken.
Software patches from other vendors
In addition to Microsoft, other vendors have released security updates over the past few weeks, fixing several vulnerabilities, including: