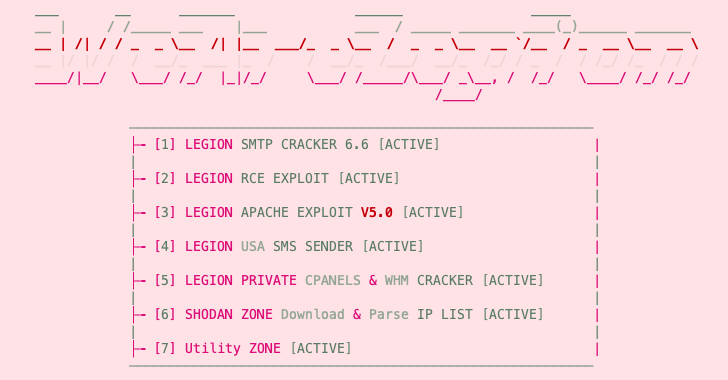
An emerging Python-based credential harvester and a hacking tool named Legion is marketed via Telegram as a way for attackers to compromise and further exploit various online services.
According to Cado Labs, Legion can enumerate vulnerable SMTP servers, perform remote code execution (RCE) attacks, exploit unpatched versions of Apache, and compromise cPanel and WebHost Manager (WHM) accounts. Contains modules for brute force attacks.
This malware is suspected to be linked to another malware family called AndroxGh0st, first documented in December 2022 by cloud security service provider Racework.
Cybersecurity firm SentinelOne revealed in an analysis released late last month that AndroxGh0st is part of a comprehensive set of tools called AlienFox provided to attackers to steal API keys and secrets from cloud services. I made it
As security researcher Matt Muir told The Hacker News: “The developers of these tools often steal each other’s code, making it difficult to attribute to any particular group.”
In addition to using Telegram as a data extraction point, Legion is designed to exploit web servers running content management systems (CMS), PHP, or PHP-based frameworks such as Laravel.
“You can get credentials for a wide range of web services, including email providers, cloud service providers, server management systems, databases, and payment platforms like Stripe and PayPal,” says Cado Labs.
Other covered services include SendGrid, Twilio, Nexmo, AWS, Mailgun, Plivo, ClickSend, Mandrill, Mailjet, MessageBird, Vonage, Exotel, OneSignal, Clickatell and TokBox.
The main purpose of this malware is to allow attackers to hijack services and weaponize their infrastructure for subsequent attacks, including launching opportunistic phishing campaigns.
The main purpose of this malware is to allow attackers to hijack services and weaponize their infrastructure for subsequent attacks, such as increasing mass spam and opportunistic phishing campaigns.
The cybersecurity firm also said it found a YouTube channel containing tutorial videos on how to use Legion, suggesting that “the tool is widely distributed and likely a paid malware.” Created June 15, 2021, the YouTube channel is still active at the time of writing.
Additionally, Legion obtains AWS credentials from insecure or misconfigured web servers to deliver SMS spam messages to users of US mobile networks such as AT&T, Sprint, T-Mobile, Verizon, and Virgin .
Master the Art of Dark Web Intelligence Gathering
Learn the art of extracting threat intelligence from the dark web – join us for this expert-led webinar!
Save my seat!
Security researcher Matt Muir said: “Then use a rudimentary number generation function to create a list of phone numbers to target.”
In addition, Legion obtains AWS credentials from insecure or misconfigured web servers and uses stolen SMTP credentials to compromise US mobile networks such as AT&T, Sprint, T-Mobile, Verizon and Virgin. May deliver SMS spam messages to users.
“To do this, the malware retrieves the user-selected US state area code from the website www.randomphonenumbers.[.]com,” said Muir.
Another notable aspect of Legion is its ability to exploit well-known PHP vulnerabilities to register persistent remote access web shells and execute malicious code.
The origin of the threat actor behind this tool (also known on Telegram as ‘forzatools’) remains unknown, but the presence of Indonesian language comments in the source code suggests that the developer is Indonesian. or may be based in Indonesia.
“Because this malware relies heavily on misconfigurations in web server technologies and frameworks such as Laravel, users of these technologies should review their existing security processes to ensure sensitive information is stored properly. I encourage you to check it out,” said Muir.









